IIA-CIA-Part3 Exam Dumps - Internal Audit Function
Searching for workable clues to ace the IIA IIA-CIA-Part3 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s IIA-CIA-Part3 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
Which of the following IT-related activities is most commonly performed by the second line of defense?
A organization finalized a contract in which a vendor is expected to design, procure, and construct a power substation for $3,000,000. In this scenario, the organization agreed to which of the following types of contracts?
Which of the following actions is likely to reduce the risk of violating transfer pricing regulations?
Which of the following risks would involve individuals attacking an oil company’s IT system as a sign of solidarity against drilling in a local area?
An organization decided to outsource its human resources function. As part of its process migration, the organization is implementing controls over sensitive employee data.
What would be the most appropriate directive control in this area?
According to The IIA's Three Lines Model, which of the following IT security activities is commonly shared by all three lines?
An internal auditor found the following information while reviewing the monthly financial siatements for a wholesaler of safety
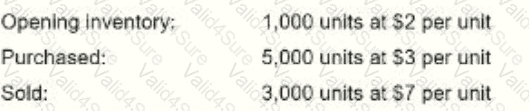
The cost of goods sold was reported at $8,500. Which of the following inventory methods was used to derive this value?