400-007 Exam Dumps - Cisco Certified Design Expert (CCDE v3.1)
Searching for workable clues to ace the Cisco 400-007 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s 400-007 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
A network design includes a long signaling delay in notifying the Layer 3 control plane that an interface has failed. Which two of these actions would reduce that delay? (Choose two.)
Company XYZ is migrating their existing network to IPv6. Some access layer switches do not support IPv6, while core and distribution switches fully support unicast and multicast routing. The company wants to minimize cost of the migration. Which migration strategy should be used?
Which two statements describe network automation and network orchestration? (Choose two.)
Which parameter is the most important factor to consider when deciding service placement in a cloud solution?
Refer to the exhibit.
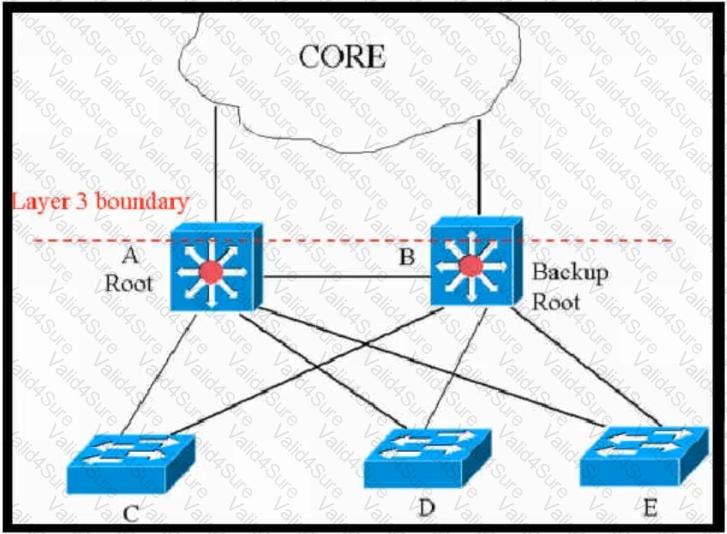
This network is running legacy STP 802.1d. Assuming "hello_timer" is fixed to 2 seconds, which parameters can be modified to speed up convergence times after single link/node failure?
SDN emerged as a technology trend that attracted many industries to move from traditional networks to SDN. Which challenge is solved by SDN for cloud service providers?
You have been asked to design a remote access VPN solution to support up to 2000 devices. You must ensure that only corporate assets are allowed to connect to the VPN, and users must authenticate to gain access based on their user role. Users must use a password that they are already using to access existing applications. A user may not always use the same device to access the VPN. Which two options combined meet the requirements? (Choose two)