400-007 Exam Dumps - Cisco Certified Design Expert (CCDE v3.1)
Searching for workable clues to ace the Cisco 400-007 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s 400-007 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
The SD-WAN architecture is composed of separate orchestration, management, control, and data planes. Which activity happens at the orchestration plane?
The goal for any network designer is to strive to build a resilient network that adapts to changing conditions rapidly with minimal impact on the services running over the network. A resilient network can adapt to failures, but which soft failure can be harder to define and detect?
What is a disadvantage of the traditional three-tier architecture model when east-west traffic between different pods must go through the distribution and core layers?
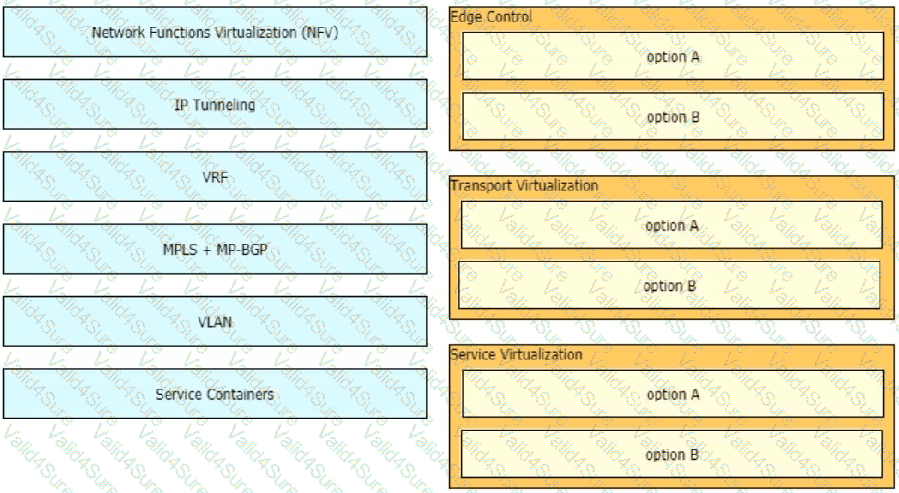
Drag and drop the end-to-end network virtualization elements from the left onto the correct network areas on the right.
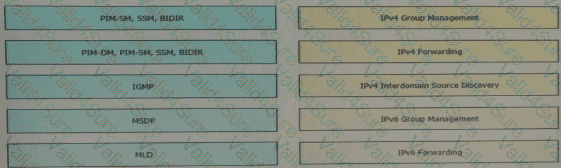
Drag and drop the multicast protocols from the left onto the current design situation on the right.
Refer to the exhibit.
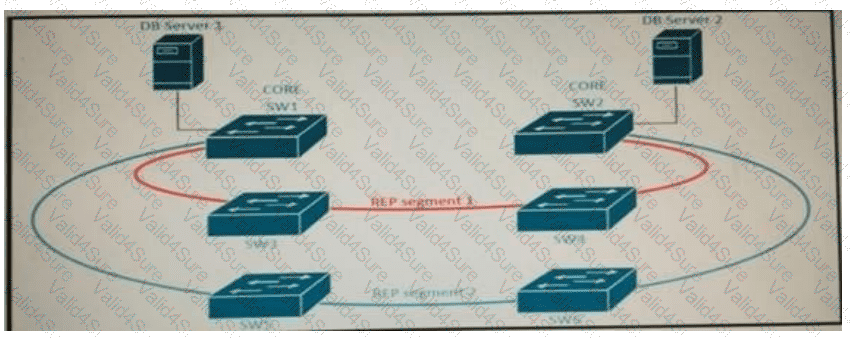
Refer to the exhibit. A new high availability DB server cluster is installed in the network. These two servers require high bandwidth and low latency Layer 2 connectivity for database replication.
Which solution supports these requirements?
A healthcare provider discovers that protected health information of patients was altered without patient consent. The healthcare provider is subject to HIPAA compliance and is required to protect PHI data. Which type of security safeguard should be implemented to resolve this issue?
You want to mitigate failures that are caused by STP loops that occur before UDLD detects the failure or that are caused by a device that is no longer sending BPDUs. Which mechanism do you use along with UDLD?
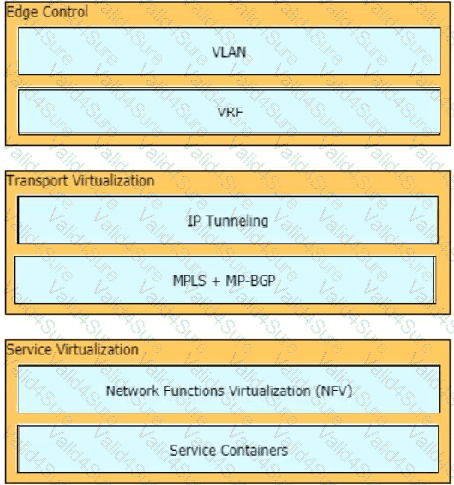 Graphical user interface
Description automatically generated with medium confidence
Graphical user interface
Description automatically generated with medium confidence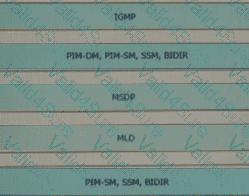 A picture containing table
Description automatically generated
A picture containing table
Description automatically generated