350-401 Exam Dumps - Implementing Cisco Enterprise Network Core Technologies (350-401 ENCOR)
Searching for workable clues to ace the Cisco 350-401 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s 350-401 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
In which forms can Cisco Catalyst SD-WAN routers be deployed at the perimeter of a site to provide SD-WAN services?
Which configuration enables a Cisco router lo send information to a TACACS+ server for individual EXEC commands associated with privilege level 15?
Which mobility role is assigned to a client in the client table of the new controller after a Layer 3 roam?
Refer to the exhibit.
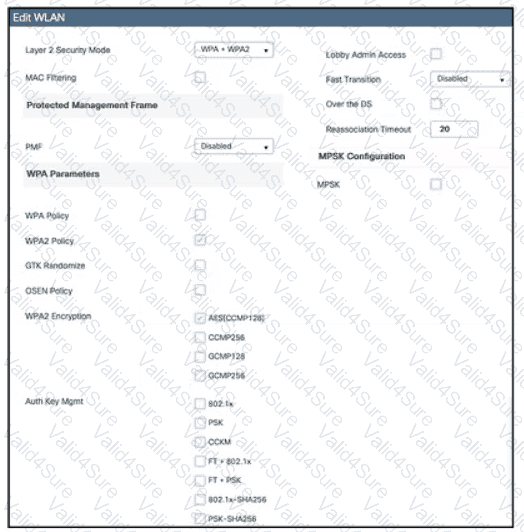
Which action must be taken to configure a WLAN for WPA2-AES with PSK and allow only 802.11r-capable clients to connect?
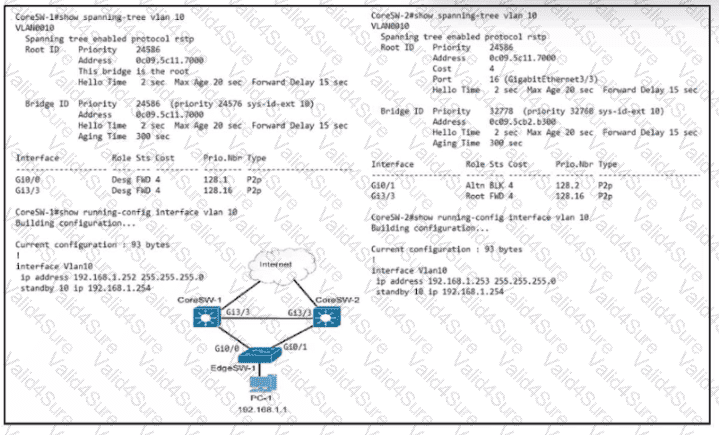
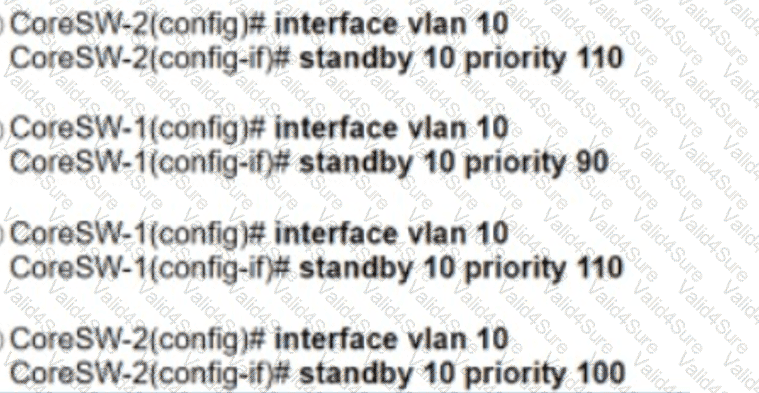
Refer to the exhibit. Which configuration causes the traffic from PC-1 to the internet to use the link between CoreSW-1 and CoreSW-2 when both switches are up?
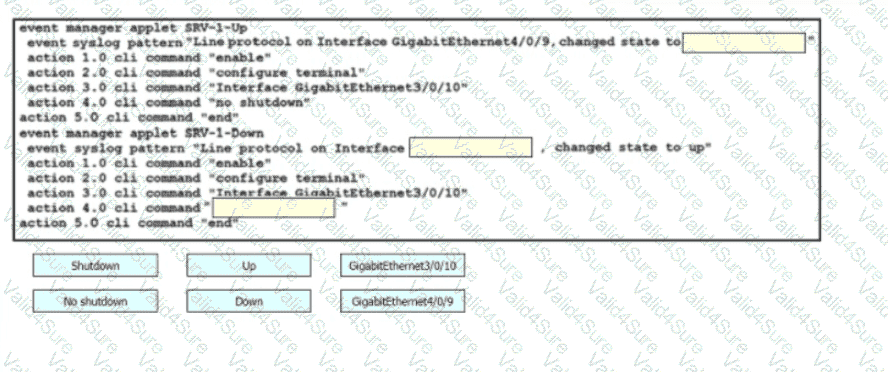
Drag and drop the snippets onto the blanks within the code to construct a script that brings up the failover Ethernet port if the primary port goes down and also shuts down the failover port when the primary returns to service. Not all options are used.
Which protocol does Cisco Catalyst SD-WAN use to protect control plane communication?