JN0-650 Exam Dumps - Enterprise Routing and Switching - Professional (JNCIP-ENT)
Searching for workable clues to ace the Juniper JN0-650 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s JN0-650 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
According to IETF standards, which two statements are correct about EVPN/VXLAN deployments? (Choose two.)
Exhibit.
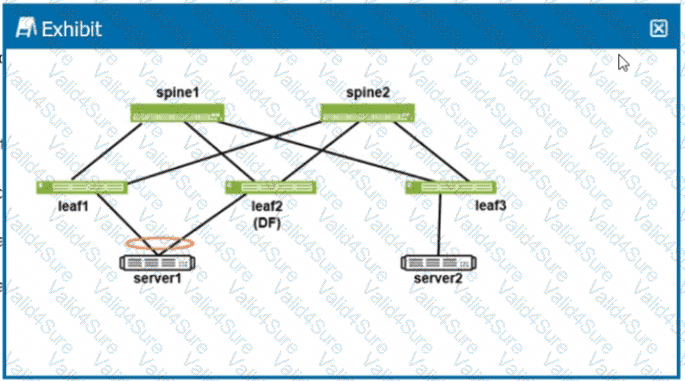
Referring to the exhibit. Ieaf2 is elected the designated forwarder
Which two statements are correct if server2 generates a broadcast frame*? (Choose two.)
While deploying class of service on an EX Series switch, what are two aspects of the scheduler? (Choose two.)
Which statement about LLDP and LLDP-MED operations on EX Series devices is correct?
You are deploying a three-stage EVPN environment with VXLAN using EX and QFX Series switches. The leaf devices will perform the gateway services. Which two statements are correct in this scenario? (Choose two.)
You are troubleshooting a multicast deployment in a network. Some multicast groups operate in PIM-ASM mode and others operate in PIM-SSM mode. While troubleshooting, you note the following:
- The network uses IGMPv2 for some segments and IGMPv3 for others.
- For group 232.1.1.1, receivers know the exact source IP of the multicast sender
- For group 239.10.10.10. receivers do not know the source address in advance.
Which two statements correctly describe the operational differences between these two modes in Junos OS? (Choose two.)
You are implementing an EVPN-VXLAN edge-routed bridging design using Layer 3 gateway operations. In this scenario, which statement is correct?
You run a multivendor switching environment where you have configured VSTP. You have 450 VLANs and notice that some of your VLANs do not function properly. How should you change the configuration to get all 450 VLANs working?