NSE7_OTS-7.2 Exam Dumps - Fortinet NSE 7 - OT Security 7.2
Searching for workable clues to ace the Fortinet NSE7_OTS-7.2 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s NSE7_OTS-7.2 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
When you create a user or host profile, which three criteria can you use? (Choose three.)
Refer to the exhibit.
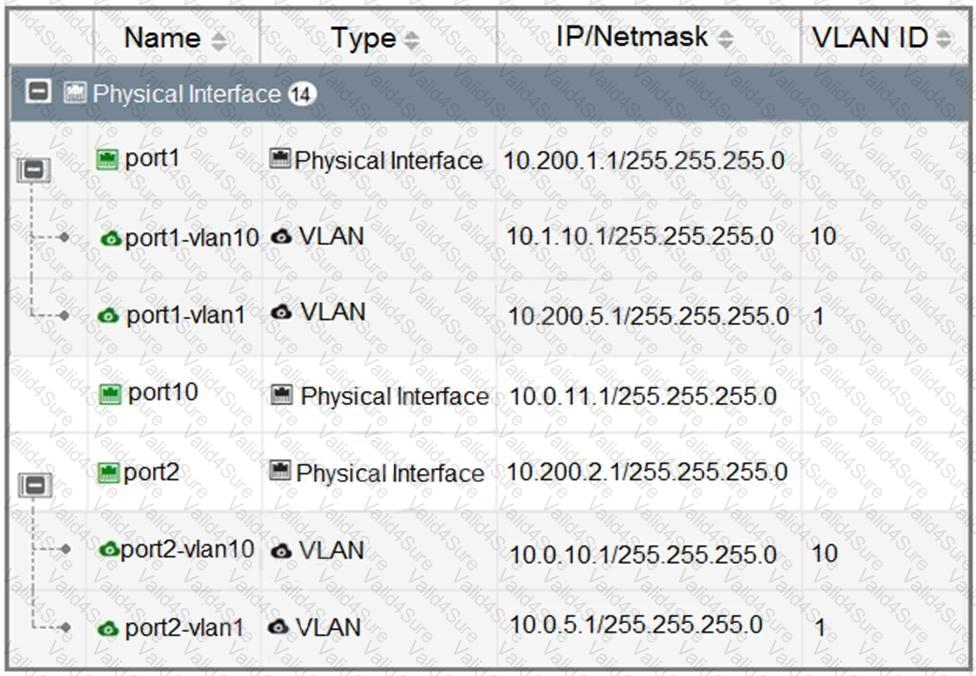
Which statement about the interfaces shown in the exhibit is true?
Refer to the exhibit.
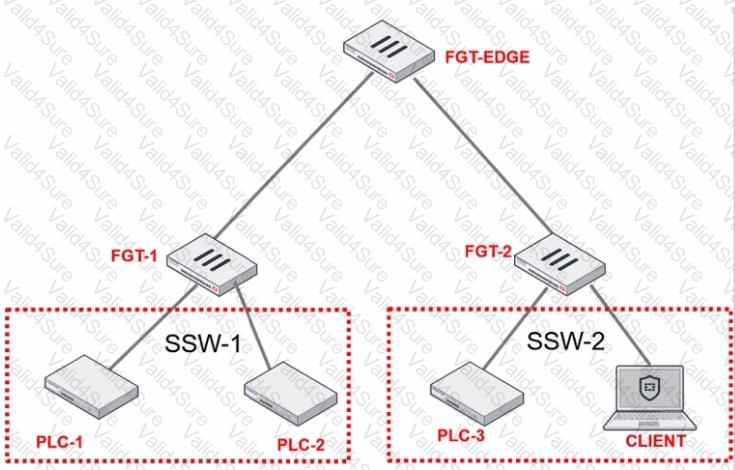
PLC-3 and CLIENT can send traffic to PLC-1 and PLC-2. FGT-2 has only one software switch (SSW-1) connecting both PLC-3 and CLIENT. PLC-3 and CLIENT cannot send traffic to each other.
Which two statements about the traffic between PCL-1 and PLC-2 are true? (Choose two.)
Which two frameworks are common to secure ICS industrial processes, including SCADA and DCS? (Choose two.)