CV0-004 Exam Dumps - CompTIA Cloud+ (V4)
Searching for workable clues to ace the CompTIA CV0-004 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s CV0-004 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
A high-usage cloud resource needs to be monitored in real time on specific events to guarantee its availability. Which of the following actions should be used to meet this requirement?
A company runs a discussion forum that caters to global users. The company's monitoring system reports that the home page suddenly is seeing elevated response times, even
though internal monitoring has reported no issues or changes. Which of the following is the most likely cause of this issue?
A cloud engineer wants resource-level visibility for billing reports. Which of the following should the cloud engineer configure?
A cloud engineer is reviewing the following Dockerfile to deploy a Python web application:
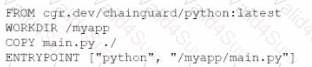
Which of the following changes should the engineer make lo the file to improve container security?
A developer is building an application that has multiple microservices that need to communicate with each other. The developer currently manually updates the IP address of each service. Which of the following best resolves the communication issue and automates the process?
Which of the following communication methods between on-premises and cloud environments would ensure minimal-to-low latency and overhead?
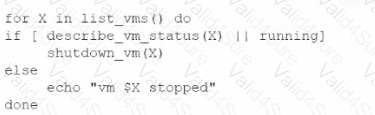
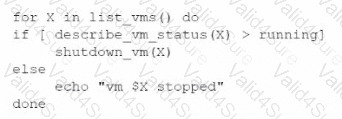
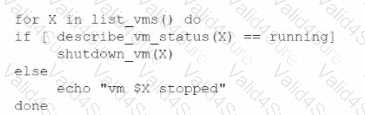
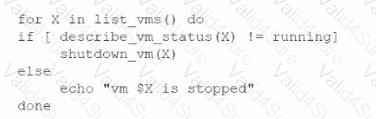
An administrator is creating a cron job that shuts down the virtual machines at night to save on costs. Which of the following is the best way to achieve this task?
A)
B)
C)
D)
Five thousand employees always access the company's public cloud-hosted web application on a daily basis during the same time frame. Some users have been reporting performance issues while attempting to connect to the web application Which of the following is the best configuration approach to resolve this issue?