220-1202 Exam Dumps - CompTIA A+ Core 2 2025 Exam
Searching for workable clues to ace the CompTIA 220-1202 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s 220-1202 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
Which of the following types of social engineering attacks sends an unsolicited text message to a user ' s mobile device?
An end user sees frequent onscreen messages from a retail site they visited a week ago. A technician investigates and determines that the pop-up blocker is turned on. Which of the following should the technician do next?
A technician thinks that an application a user downloaded from the internet may not be the legitimate one, even though the name is the same. The technician needs to confirm whether the application is legitimate. Which of the following should the technician do?
A user switches from Linux to Windows and tries to migrate data using an external USB drive. Windows prompts that the device must be formatted. It works fine on Linux. What should the user do?
A user has rooted their corporate phone to load unapproved software. Which of the following tools should the company use to prevent access to the corporate network?
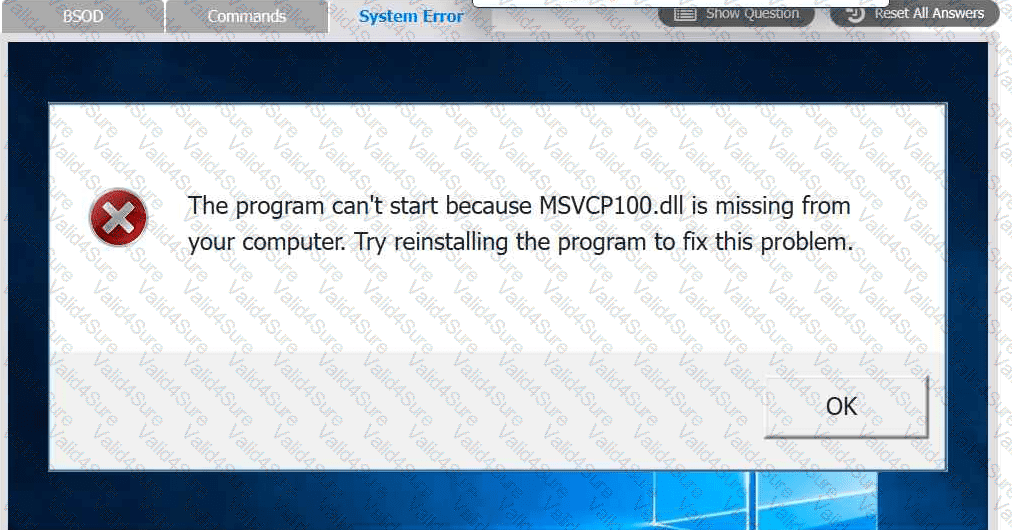
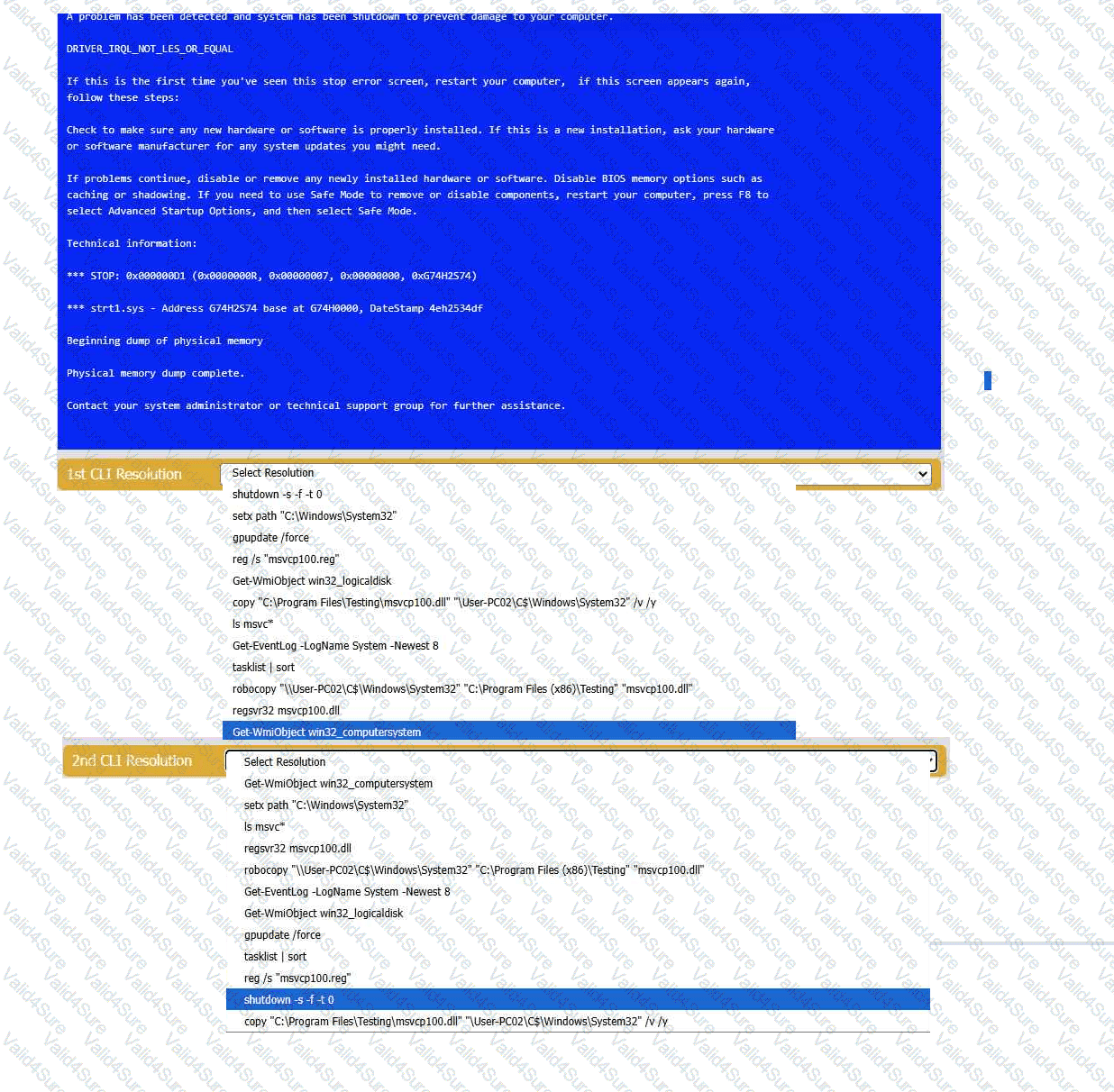
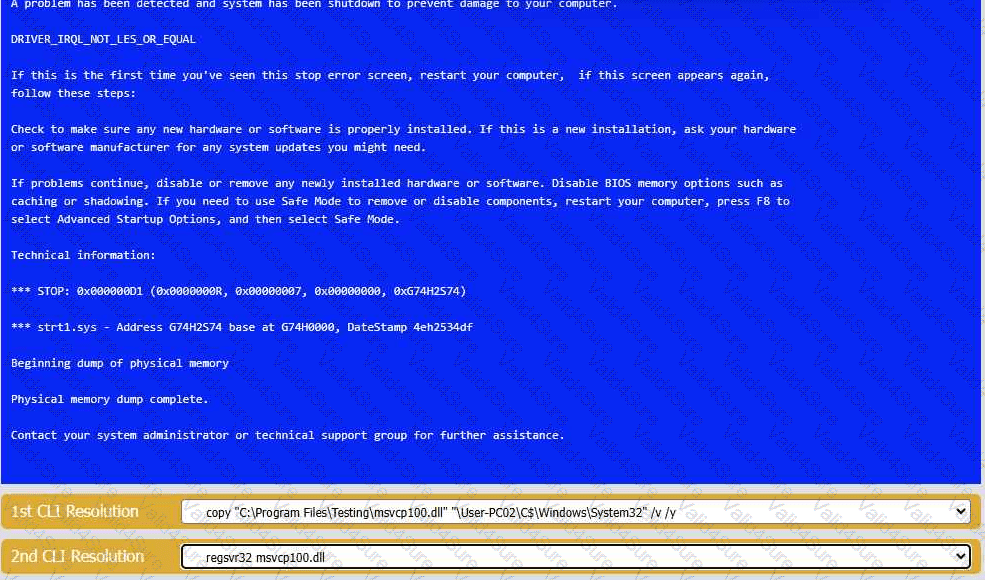
A user reports that after a recent software deployment to upgrade the Testing application, they can no longer use it. However, other employees can successfully
use the Testing program.
INSTRUCTIONS
Review the information in each tab to verify the results of the deployment and resolve
any issues discovered by selecting the:
· First command to resolve the issue
· Second command to resolve the issue
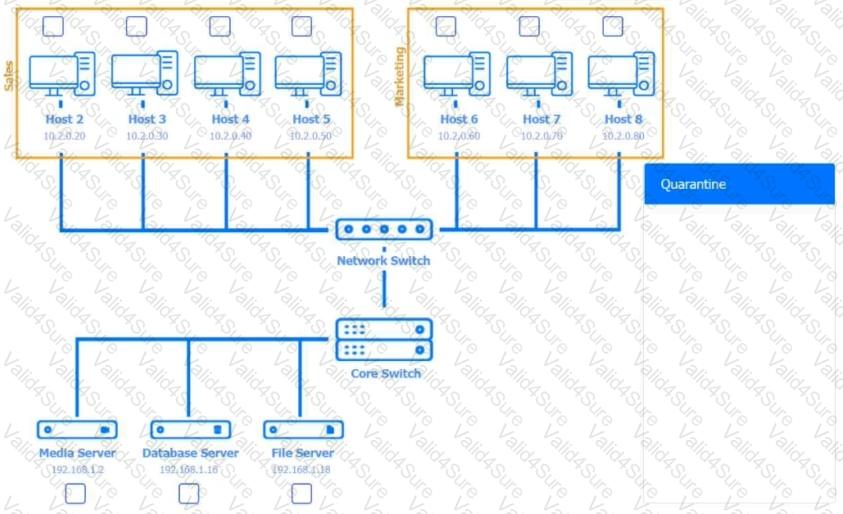
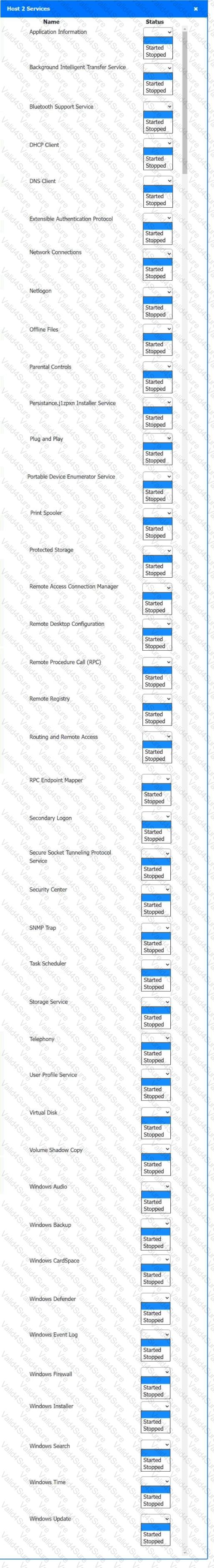
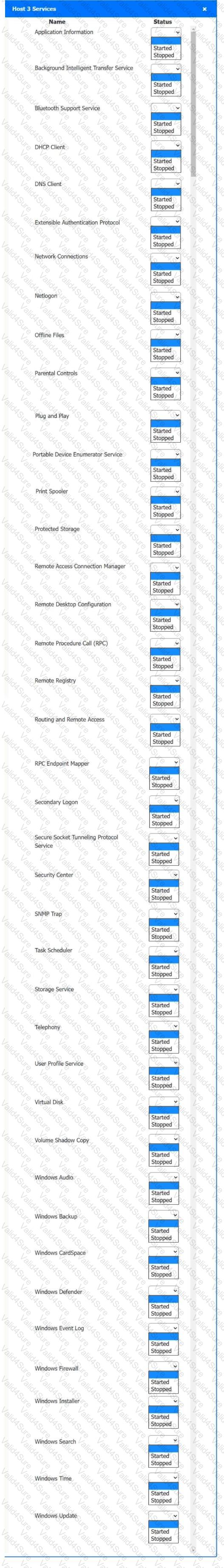
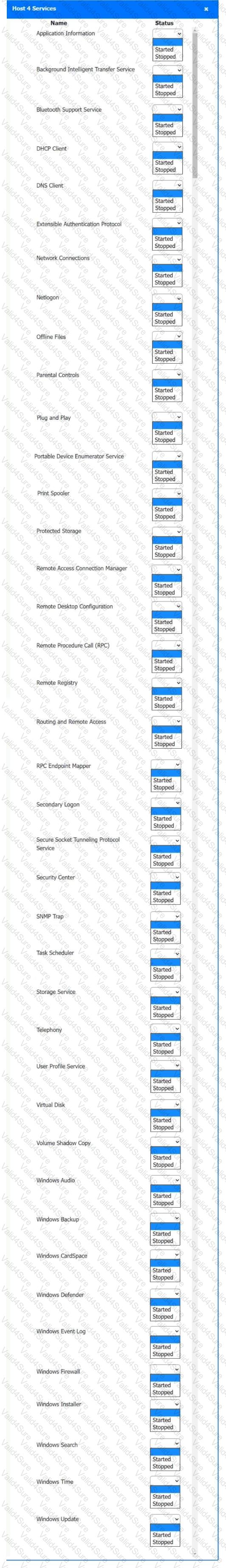
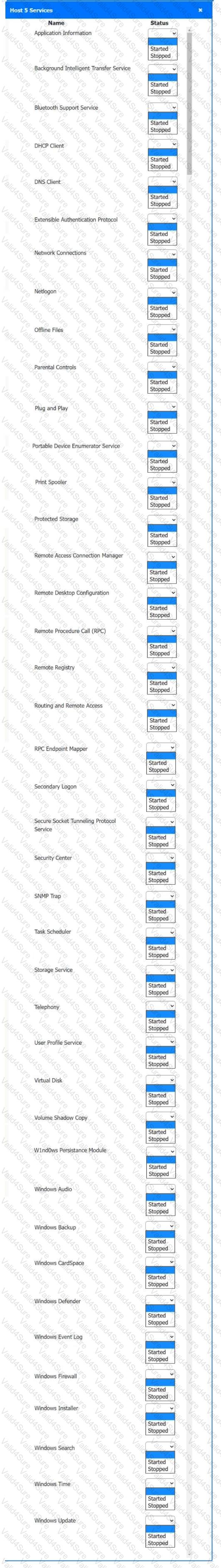
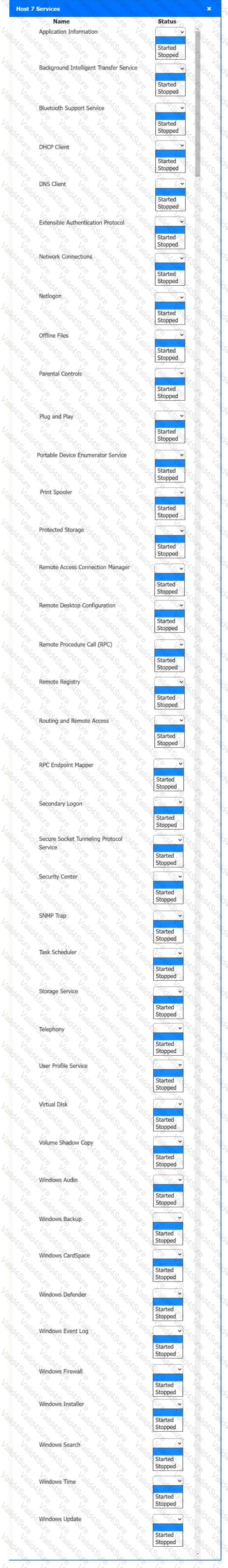
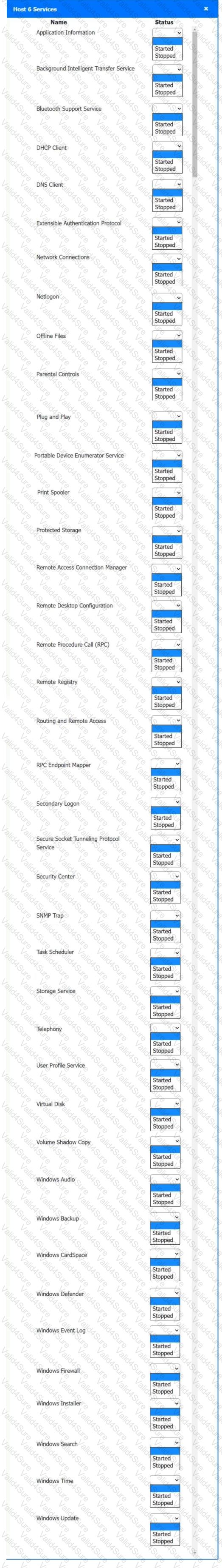
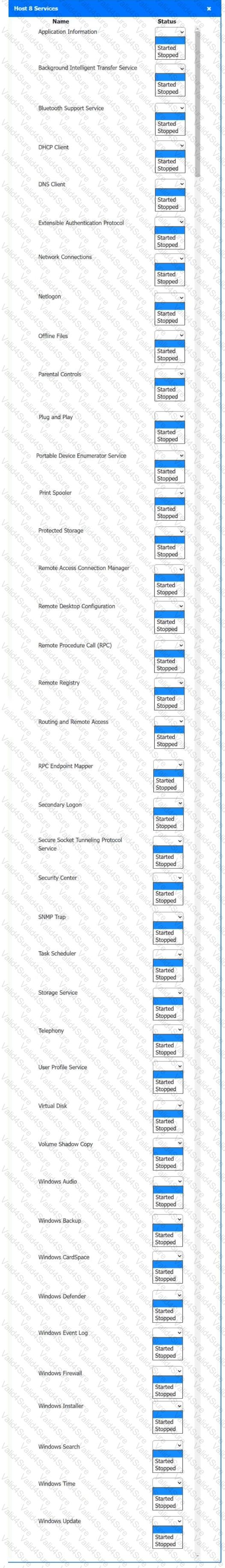
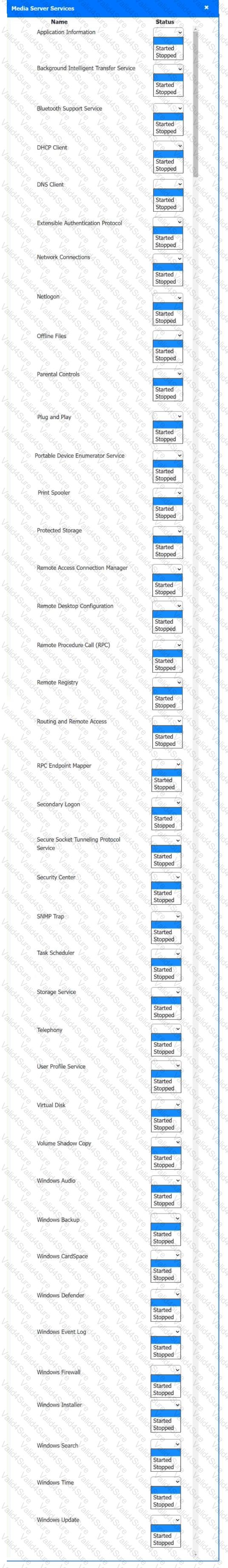
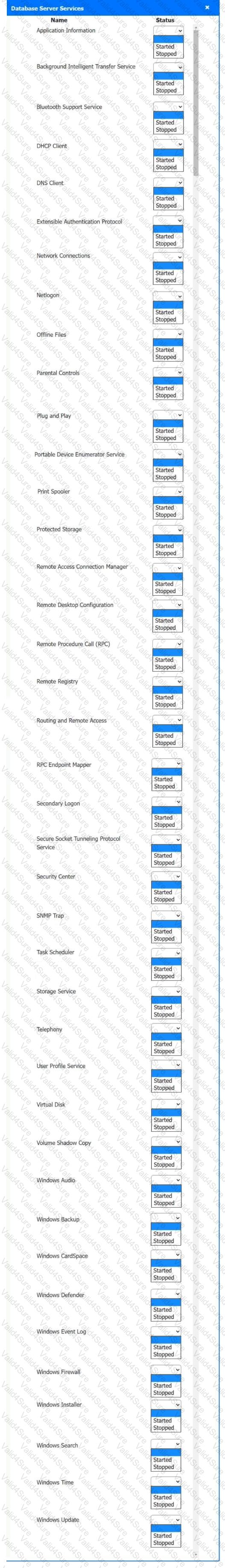
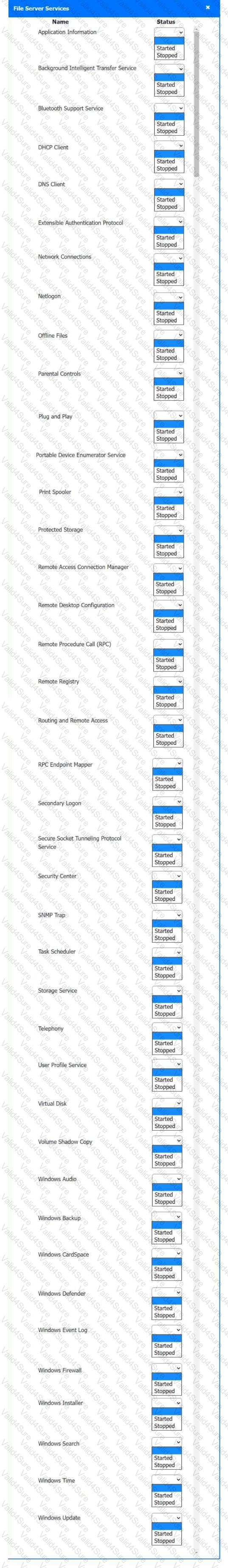
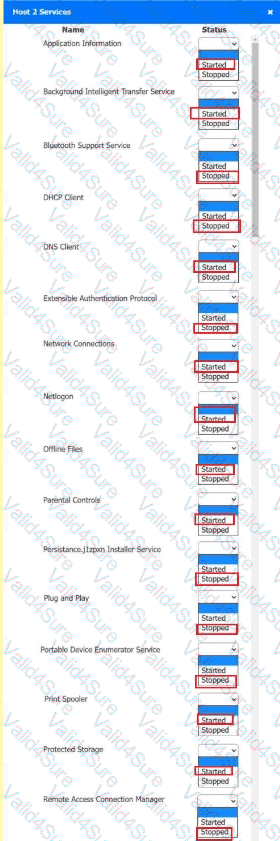
Multiple users are reporting audio issues as well as performance issues after downloading unauthorized software. You have been dispatched to identify and resolve any issues on the network using best practice procedures.
INSTRUCTIONS
Quarantine and configure the appropriate device(s) so that the users’ audio issues are resolved using best practice procedures.
Multiple devices may be selected for quarantine.
Click on a host or server to configure services.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
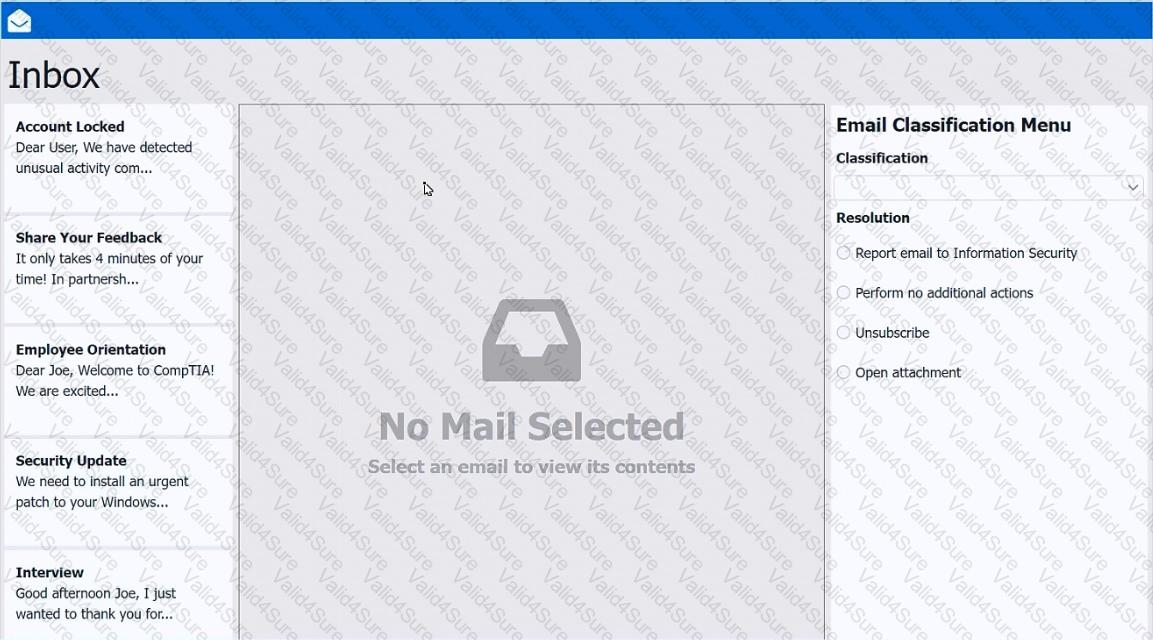
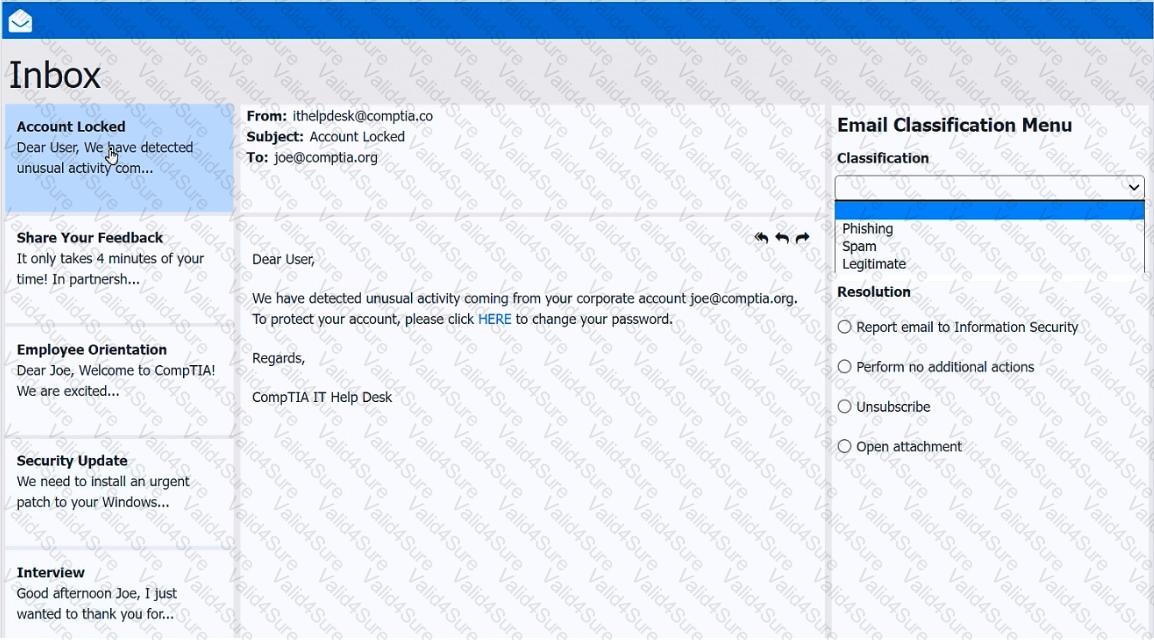
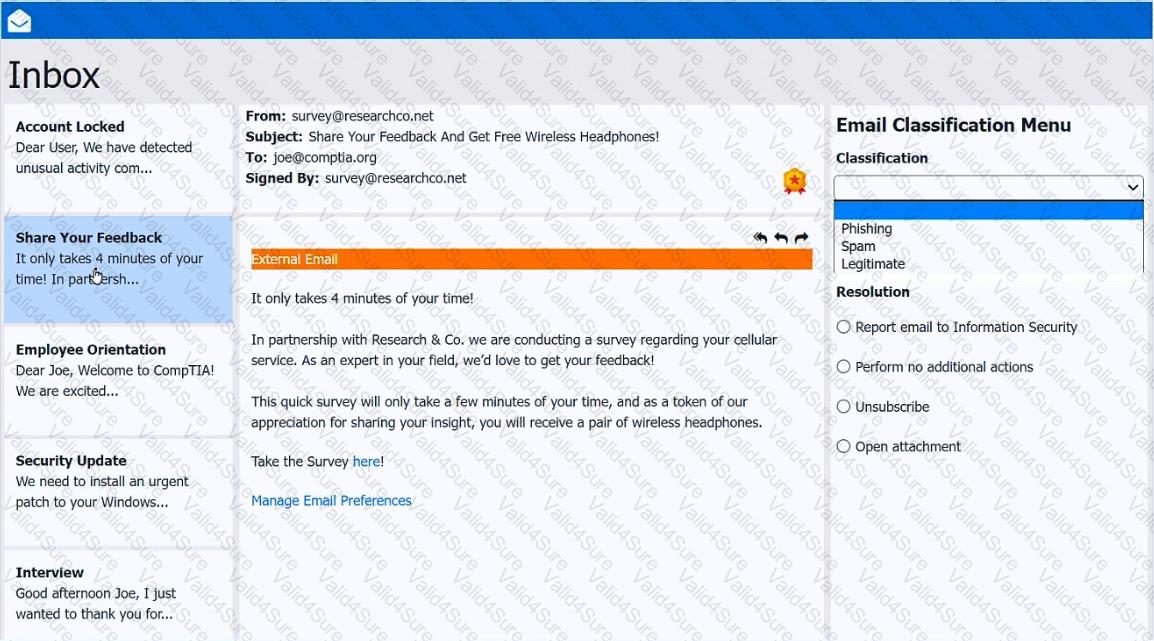
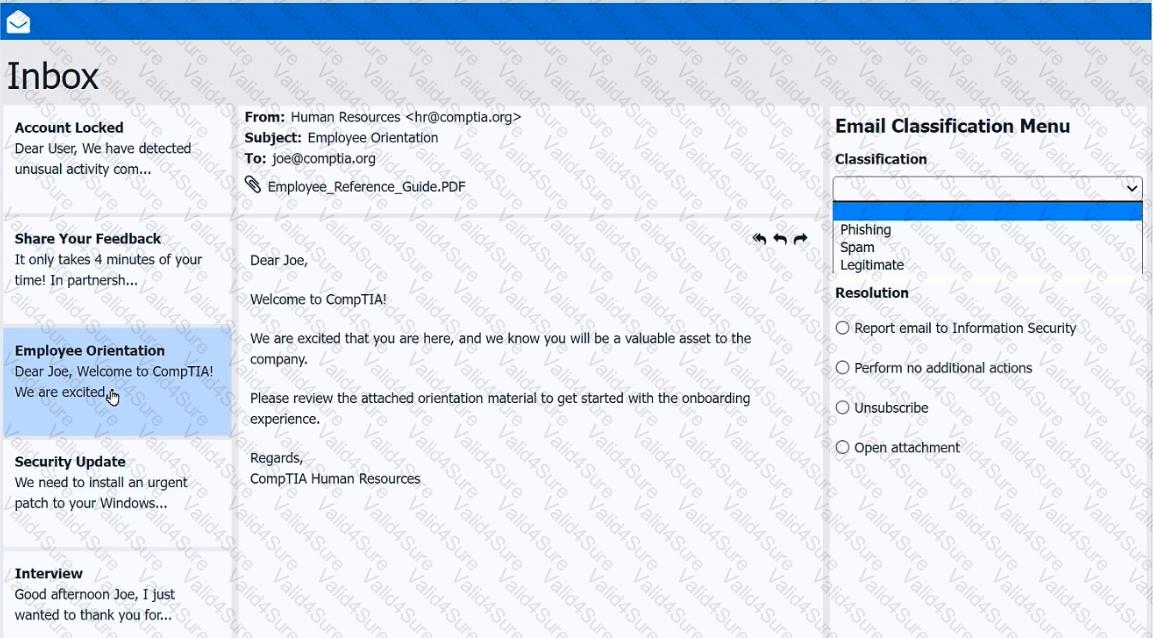
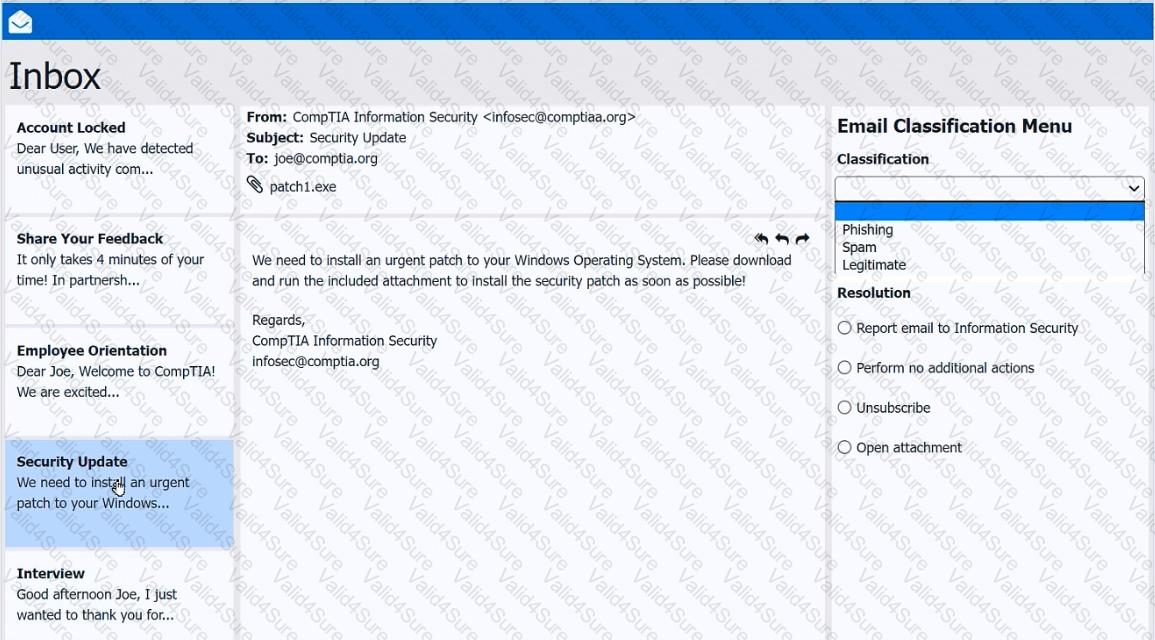
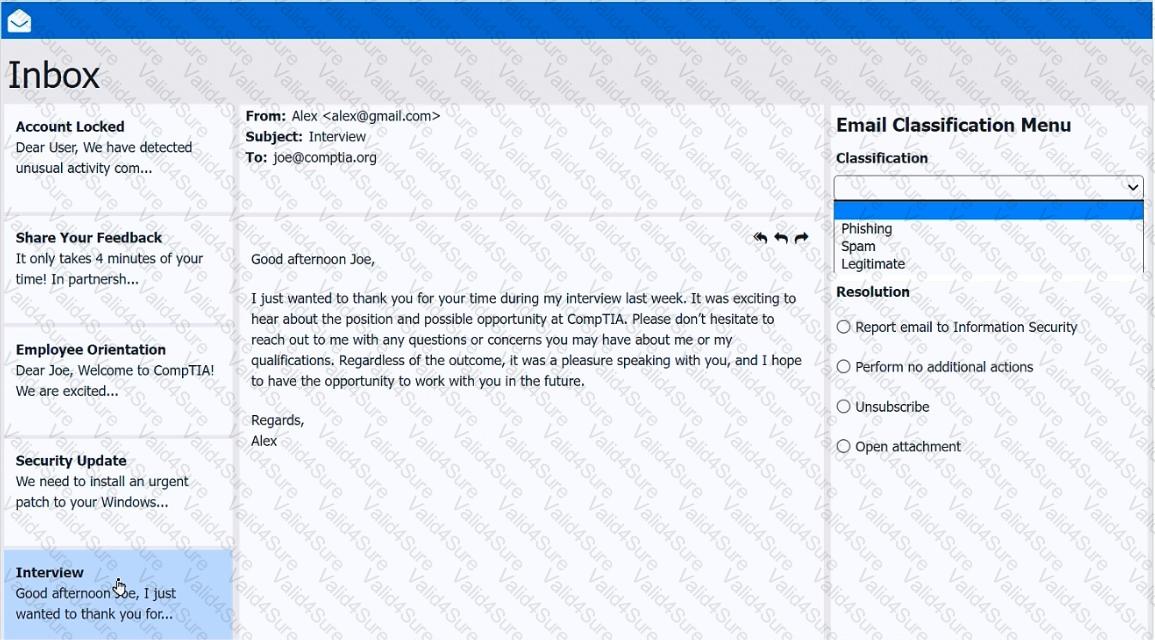
As a corporate technician, you are asked to evaluate several suspect email messages on a client ' s computer. Corporate policy requires the following:
> All phishing attempts must be reported.
> Future spam emails to users must be prevented.
INSTRUCTIONS
Review each email and perform the following within the email:
> Classify the emails
> Identify suspicious items, if applicable, in each email
> Select the appropriate resolution
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
 A screenshot of a computer AI-
A screenshot of a computer AI- 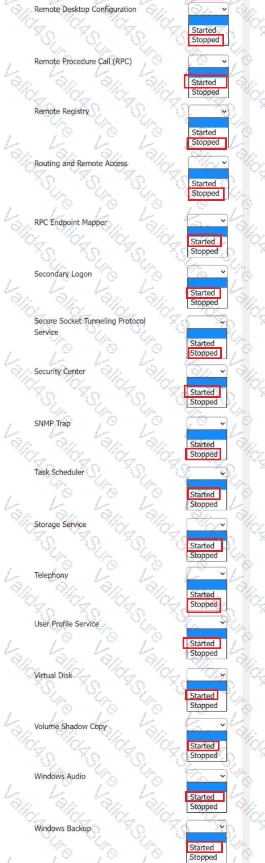 A screenshot of a computer AI-
A screenshot of a computer AI-