200-301 Exam Dumps - Implementing and Administering Cisco Solutions (200-301 CCNA) v1.1
Searching for workable clues to ace the Cisco 200-301 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s 200-301 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
Which two values or settings must be entered when configuring a new WLAN in the Cisco Wireless LAN Controller GUI? (Choose two)
An engineer must configure a WLAN using the strongest encryption type for WPA2- PSK. Which cipher fulfills the configuration requirement?
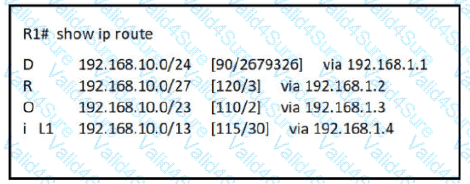
Refer to the exhibit.
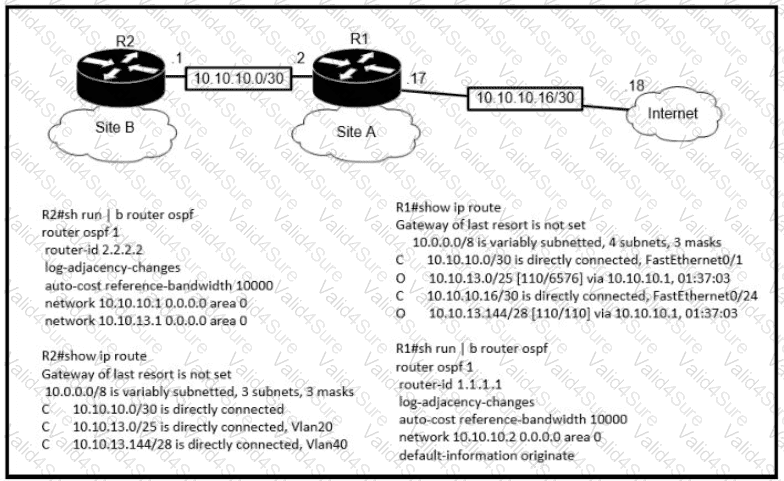
The default-information originate command is configured under the R1 OSPF configuration After testing workstations on VLAN 20 at Site B cannot reach a DNS server on the Internet Which action corrects the configuration issue?