SY0-701 Exam Dumps - CompTIA Security+ Exam 2026
Searching for workable clues to ace the CompTIA SY0-701 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s SY0-701 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
A legacy device is being decommissioned and is no longer receiving updates or patches. Which of the following describes this scenario?
An organization disabled unneeded services and placed a firewall in front of a business-critical legacy system. Which of the following best describes the actions taken by the organization?
A company is using a legacy FTP server to transfer financial data to a third party. The legacy system does not support SFTP, so a compensating control is needed to protect the sensitive, financial data in transit. Which of the following would be the most appropriate for the company to use?
A security analyst is reviewing logs and discovers the following:
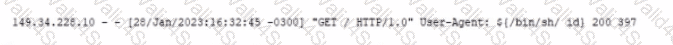
Which of the following should be used lo best mitigate this type of attack?
Which of the following should be used to select a label for a file based on the file's value, sensitivity, or applicable regulations?
Company A jointly develops a product with Company B, which is located in a different country. Company A finds out that their intellectual property is being shared with unauthorized companies. Which of the following has been breached?
An administrator is reviewing a single server's security logs and discovers the following;
Which of the following best describes the action captured in this log file?
Which of the following would be best suited for constantly changing environments?