SC-401 Exam Dumps - Administering Information Security in Microsoft 365
Searching for workable clues to ace the Microsoft SC-401 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s SC-401 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a Microsoft 365 subscription.
You have a user named User1. Several users have full access to the mailbox of User1.
Some email messages sent to User1 appear to have been read and deleted before the user viewed them.
When you search the audit log in the Microsoft Purview portal to identify who signed in to the mailbox of User1, the results are blank.
You need to ensure that you can view future sign-ins to the mailbox of User1.
Solution: You run the Set-MailboxFolderPermission -Identity " User1 " -User User1@contoso.com -AccessRights Owner command.
Does that meet the goal?
You have a Microsoft 365 E5 tenant that uses a domain named contoso.com.
A user named User 1 sends link based, branded emails that are encrypted by using Microsoft Purview Advanced Message Encryption to the recipients shown in the following table.
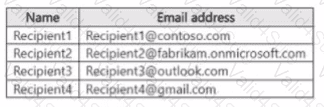
For which recipients Can User1 revoke the emails?
You have a Microsoft 365 E5 subscription that contains a device named Device1.
You need to enable Endpoint data loss prevention (Endpoint DLP) for Device1.
What should you do first in the Microsoft Purview portal?
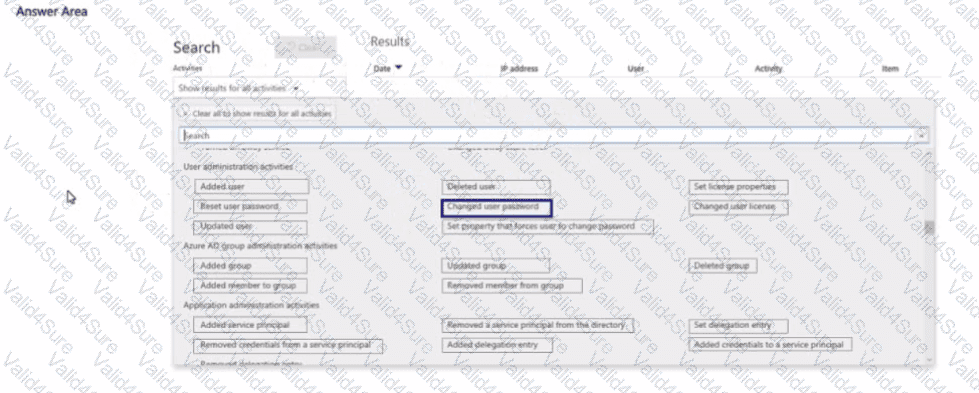
You have a Microsoft 365 subscription. Auditing is enabled.
A user named User1 is a member of a dynamic security group named Group1.
You discover that User1 is no longer a member of Group1.
You need to search the audit log to identify why User1 was removed from Group1.
Which two activities should you use in the search? To answer, select the appropriate activities in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 subscription.
You have a user named User1 Several users have full access to the mailbox of User1.
Some email messages sent to User 1 appeal to have been read and deleted before the user viewed them
When you search the audit log in the Microsoft Purview portal to identify who signed in to the mailbox of User l. the results are blank.
You need to ensure that you can view future sign-ins to the mailbox of User1.
Solution: You run the Set-AuditConfig -Workload Exchange command.
Does that meet the goal?
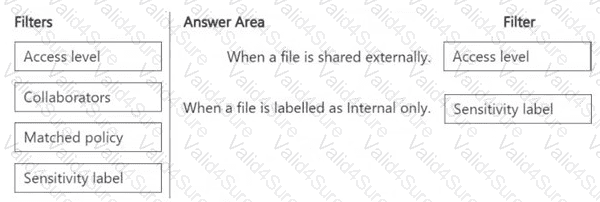
You have a Microsoft 365 E5 subscription that uses Microsoft Defender for Cloud Apps.
You plan to deploy a Defender for Cloud Apps file policy that will be triggered when the following conditions are met:
â— A file is shared externally.
â— A file is labeled as internal only.
Which filter should you use for each condition? To answer, drag the appropriate filters to the correct conditions. Each filter may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE : Each correct selection is worth one point.

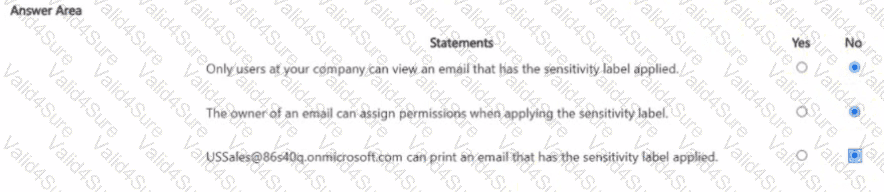
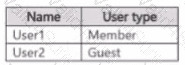
You have Microsoft 365 E5 tenant that has a domain name of 86s40q.ofimicrosoft.com. The tenant contains the users shown in the following table.
You have a published sensitivity label.
The Access control settings for the sensitivity label are configured as shown in the exhibit (Click the Exhibit tab.)

For each of the following statements, select Yes if the statement is true. Otherwise, select No.

You have a Microsoft 365 E5 subscription that contains a Microsoft SharePoint Online site named Site1. Site1 contains the files shown in the following table.

In the Microsoft Purview portal, you create a content search named Conlent1 and configure the search conditions as shown in the following exhibit.

Which files will be returned by Content1?