Practitioner Exam Dumps - Palo Alto Networks Cybersecurity Practitioner (PCCP)
Searching for workable clues to ace the Paloalto Networks Practitioner Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s Practitioner PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
Which VM-Series virtual firewall cloud deployment use case reduces your environment's attack surface?
What are two examples of an attacker using social engineering? (Choose two.)
In addition to local analysis, what can send unknown files to WildFire for discovery and deeper analysis to rapidly detect potentially unknown malware?
What are the two most prominent characteristics of the malware type rootkit? (Choose two.)
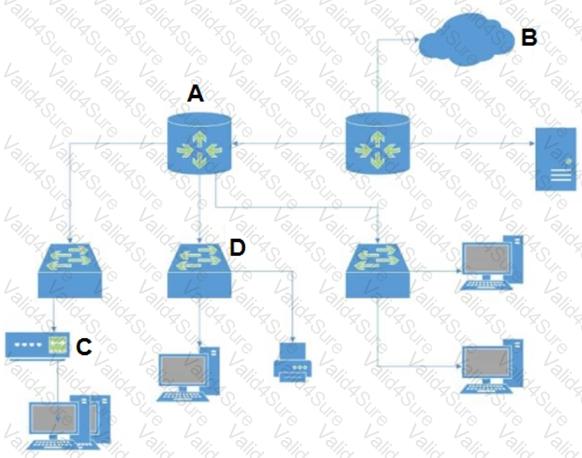
Which security component can detect command-and-control traffic sent from multiple endpoints within a corporate data center?
What should a security operations engineer do if they are presented with an encoded string during an incident investigation?