NSE4_FGT_AD-7.6 Exam Dumps - Fortinet NSE 4 - FortiOS 7.6 Administrator
Searching for workable clues to ace the Fortinet NSE4_FGT_AD-7.6 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s NSE4_FGT_AD-7.6 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
You have created a web filter profile named restrictmedia-profile with a daily category usage quota.
When you are adding the profile to the firewall policy, the restrict_media-profile is not listed in the available web profile drop down.
What could be the reason?
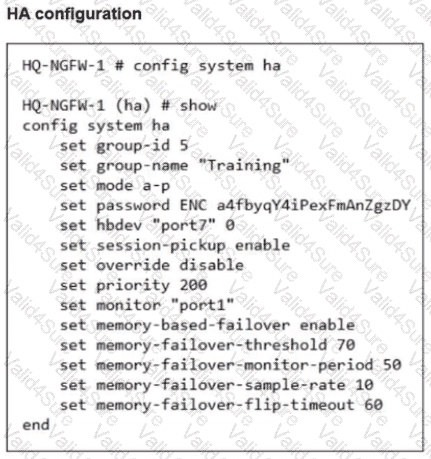
What is the primary FortiGate election process when the HA override setting is enabled? (Choose one answer)
Refer to the exhibit.
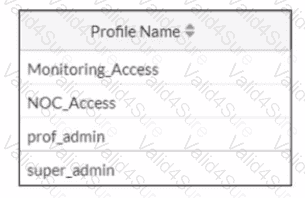
The NOC team connects to the FortiGate GUI with the NOC_Access admin profile. They request that their GUI sessions do not disconnect too early during inactivity. What must the administrator configure to answer this specific request from the NOC team?
Refer to the exhibit.
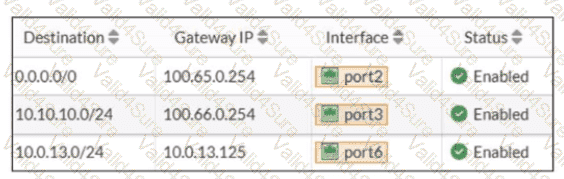
Based on the routing table shown in the exhibit, which two statements are true? (Choose two.)
Refer to the exhibits.
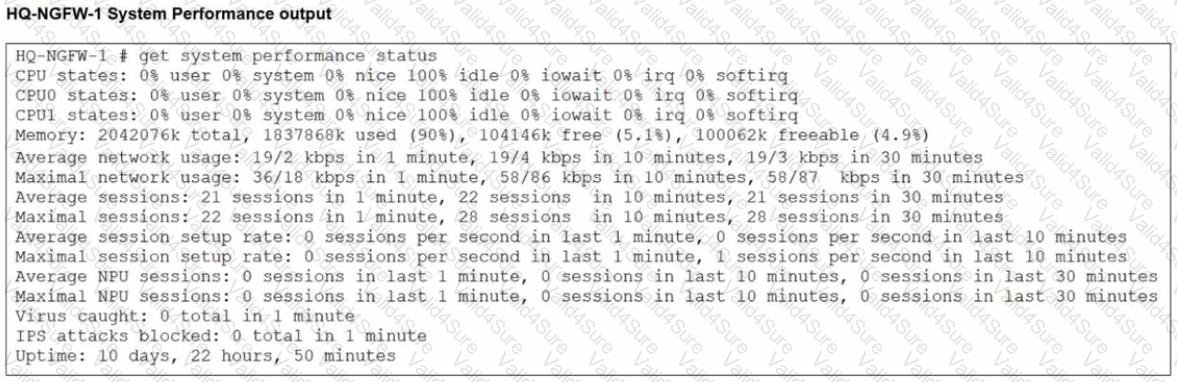
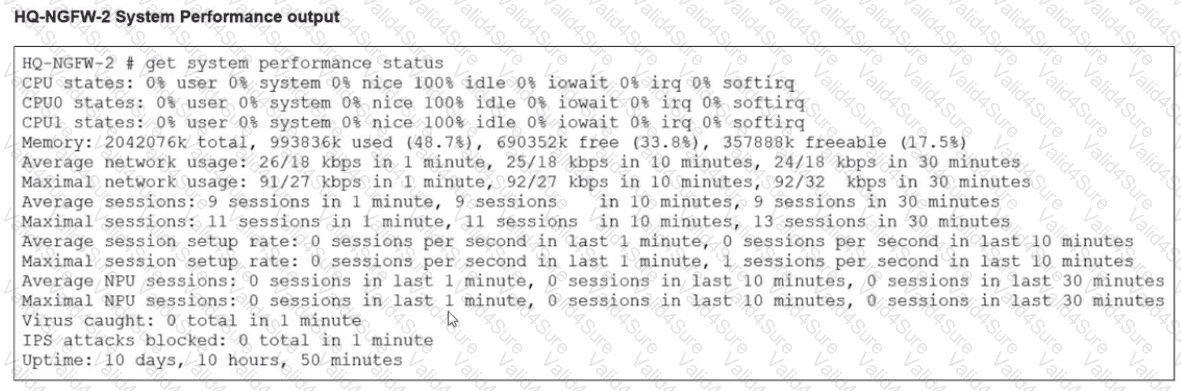
An administrator has observed the performance status outputs on an HA cluster for 55 seconds.
Which FortiGate is the primary?