CPIM-8.0 Exam Dumps - Certified in Planning and Inventory Management (CPIM 8.0)
Searching for workable clues to ace the APICS CPIM-8.0 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s CPIM-8.0 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
An OpenID Connect (OIDC) authorization server received two requests from a client. The server identifies the request as replay attack and rejects the request. Which of the following BEST describes these requests?
The cost accountant has discovered a consistent overage in actual run time for one operation. This information should be sent first to the:
The time spent In queue by a specific manufacturing job is determined by which of the following factors related to the order?
Which of the following actions provides the BEST evidence for forensic analysis of powered-off device?
An organization’s security assessment recommended expanding its secure software development framework to include testing Commercial Off-The-Shelf (COTS) products before deploying those products in production. What is the MOST likely reason for this recommendation?
An organization routes traffic between two of its sites using non-revenue network paths provided by peers on an Internet exchange point. What is the MOST appropriate recommendation the organization ' s security staff can make to prevent a compromise?
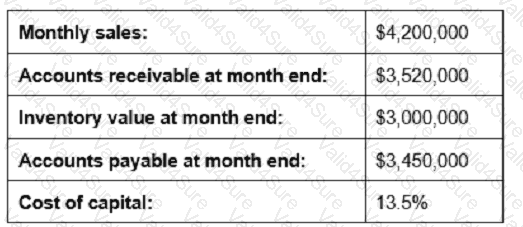
Given the information below, reducing which measure by 10% would contribute most to shortening the cash-to-cash cycle time?
An information security auditor is creating an audit program to assess endpoint security controls for portable storage media movement. Which type of control will MOST likely be part of the program?