300-745 Exam Dumps - Designing Cisco Security Infrastructure (300-745 SDSI) v1.0
Searching for workable clues to ace the Cisco 300-745 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s 300-745 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
A bank experienced challenges with compromised endpoints gaining access to the internal network. To enhance security, the bank wants to ensure that all endpoints are scanned for compliance checks before being allowed to access the network. Which action achieves the level of security and control?
A global energy company moved a monolithic application from the data center to public cloud. Over time, the company added many capabilities to the application, and it is now difficult for the application team to scale it. The application owner decided to modernize the application by moving to a Kubernetes cluster. However, he wants to ensure that the new application architecture provides a container network interface that is scalable, offers options for cloud-native security, and helps with visibility and observability. Which solution must be used to accomplish the task?
Considering recent cybersecurity threats, a company wants to improve the process for identifying, assessing, and managing risks with a comprehensive and holistic approach. Which framework must be used to meet these requirements?
After deploying a new API, the security team must identify the components of the application that are exposed to the internet and whether there are application authentication risks. Which technology must be deployed to discover the applications services and monitor for authentication issues?
Refer to the exhibit.
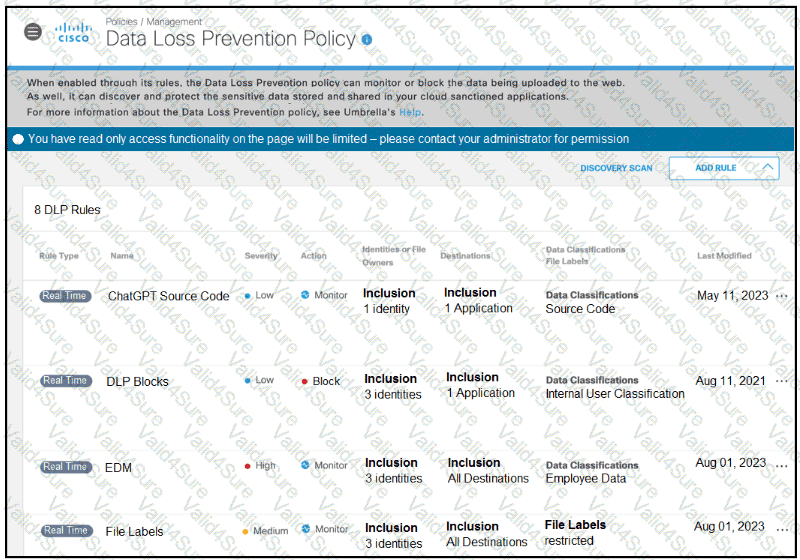
A software developer noticed that the application source code had been found on the internet. To avoid such an incident from happening again, the developer applied a DLP policy to prevent from uploading source code into generative AI tool like ChatGPT. When testing the policy, the developer noticed that it is still possible for the source code to be uploaded. Which action must the developer take to prevent this issue?