300-215 Exam Dumps - Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR)
Searching for workable clues to ace the Cisco 300-215 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s 300-215 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
During a routine inspection of system logs, a security analyst notices an entry where Microsoft Word initiated a PowerShell command with encoded arguments. Given that the user's role does not involve scripting or advanced document processing, which action should the analyst take to analyze this output for potential indicators of compromise?
Which two tools conduct network traffic analysis in the absence of a graphical user interface? (Choose two.)
A threat hunter must analyze the threat intelligence report on APT29 and identify whether the threat actor is on the Windows machines of the customer network. According to the report the user executes a malicious file on the victim machine that establishes a C? connection over port 53 Afterward, the attacker uses a CI.I to stage and exfiltrate business data. Which two types of logs enable the threat hunter to accomplish the task? (Choose two.)
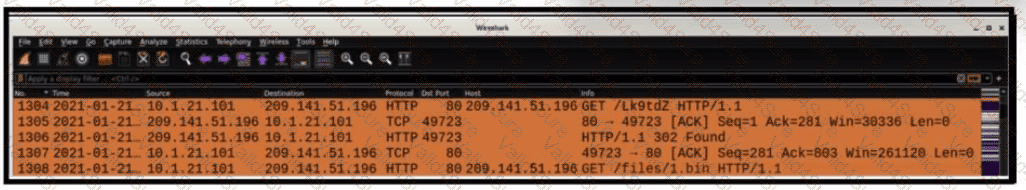
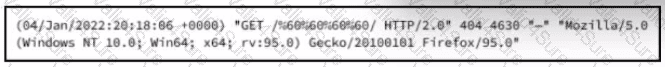
Refer to the exhibit.
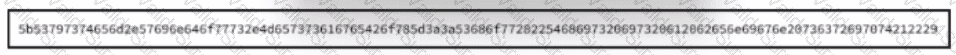
Which encoding method is used to obfuscate the script?
An attacker modifies a malicious file named TOPSECRET0523619132 by changing its file extension from a .png to a doc in an attempt to evade detection. Which technique is being used to disguise the file?