250-587 Exam Dumps - Symantec Data Loss Prevention 16.x Administration Technical Specialist
Searching for workable clues to ace the Symantec 250-587 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s 250-587 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
Which option is an accurate use case for Information Centric Encryption (ICE)?
Refer to the exhibit.
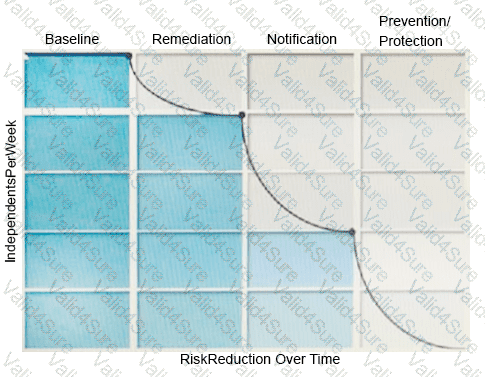
What activity should occur during the baseline phase, according to the risk reduction model?
Which option correctly describes the two-tier installation type for Symantec DLP?
What are three features that are available for Network Discover File System High-Speed Discover (FS-HSD) scans but are NOT available for Network Discover (regular or legacy) File System scans?
Which of the following actions can you implement ONLY as a Smart Response rule (and not as an automates response rule)?