250-587 Exam Dumps - Symantec Data Loss Prevention 16.x Administration Technical Specialist
Searching for workable clues to ace the Symantec 250-587 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s 250-587 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
Which two detection technology options run on the DLP agent? (Choose two.)
An organization wants to restrict employees to copy files only a specific set of USB thumb drives owned by the organization.
Which detection method should the organization use to meet this requirement?
Which two (2) detection technology options run ONLY on detection servers and NOT on endpoint agents? (Choose two.)
Under the “System Overview†in the Enforce management console, the status of a Network Monitor detection server is shown as “Running Selected.†The Network Monitor server’s event logs indicate that the packet capture and filereader processes are crashing.
What is a possible cause for the Network Monitor server being in this state?
How should a DLP administrator change a policy that it retains the original file when an endpoint incident has detected a “copy to USB device†operation?
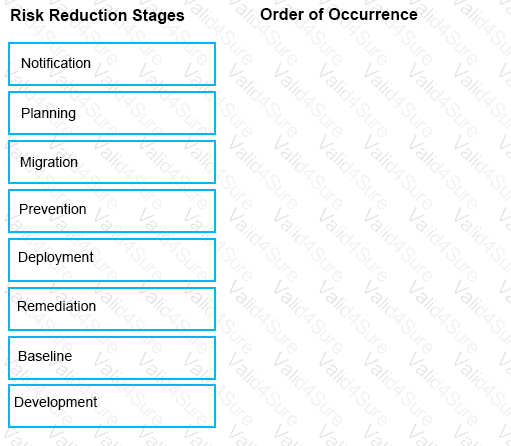
The Symantec Data Loss risk reduction approach has six stages.
Drag and drop the six correct risk reduction stages in the proper order of Occurrence column.
A DLP administrator is preparing to install Symantec DLP and has been asked to use an Oracle database provided by the Database Administration team.
Which SQL *Plus command should the administrator utilize to determine if the database is using a supported version of Oracle?