200-201 Exam Dumps - Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)
Searching for workable clues to ace the Cisco 200-201 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s 200-201 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
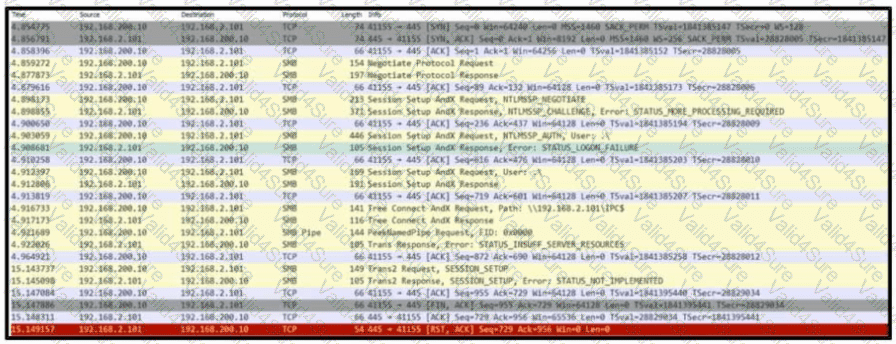
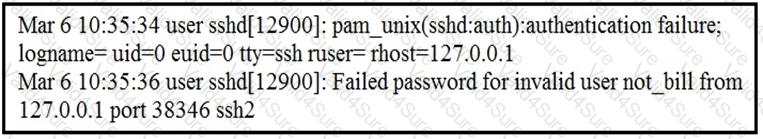
Refer to the exhibit. Based on the .pcap file, which protocol's vulnerability has been exploited to establish a session?
Which data format is the most efficient to build a baseline of traffic seen over an extended period of time?
A software development company develops high-end technology for the customer that will go through the HIPAA audit program. The technology will be hosted in the cloud, and the healthcare, employee names, and contact information will be stored on two separate logically isolated private cloud services. The patents and inventions will be hosted on a separate encrypted database. A compliance team is asked to analyze the cloud infrastructure and architecture to identify the protected data. Which two types of protected data should be identified? (Choose two.)
What are the two differences between vulnerability and exploit? (Choose two.)
What describes the impact of false-positive alerts compared to false-negative alerts?
A security engineer must protect the company from known issues that trigger adware. Recently new incident has been raised that could harm the system. Which security concepts are present in this scenario?