200-201 Exam Dumps - Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)
Searching for workable clues to ace the Cisco 200-201 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s 200-201 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
A security engineer must implement an Intrusion Prevention System (IPS) inside an organization’s DMZ. One of the requirements is the ability to block suspicious traffic in real time based on a triggered signature. The IPS will be connected behind the DMZ firewalls directly to the core switches. Which traffic integration method must be implemented to complete this project?
What is personally identifiable information that must be safeguarded from unauthorized access?
Refer to the exhibit.
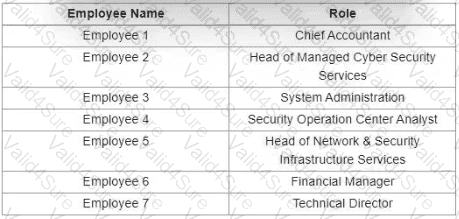
Which stakeholders must be involved when a company workstation is compromised?
Refer to the exhibit.
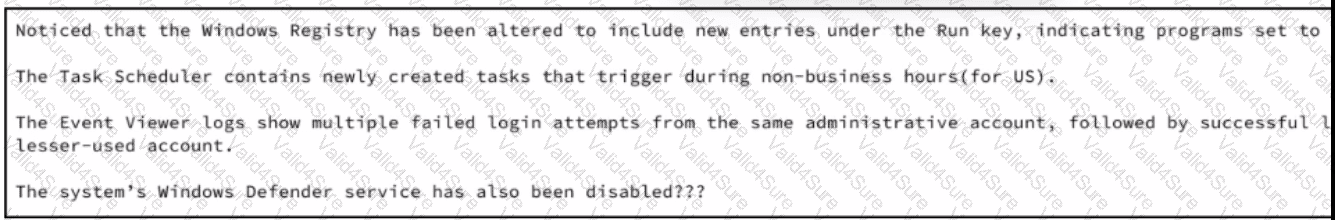
A security analyst wraps up the shift and passed open ticket notes to the night shift SOC team analyst. The ticket name in question is "Investigating suspicious activity on a Windows Server’’. Which operating system components must the analyst prioritize to uncover the attacker's persistence mechanisms?
Which vulnerability type is used to read, write, or erase information from a database?
What are two differences between tampered disk images and untampered disk images'? (Choose two.)