200-201 Exam Dumps - Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)
Searching for workable clues to ace the Cisco 200-201 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s 200-201 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
Which metric in CVSS indicates an attack that takes a destination bank account number and replaces it with a different bank account number?
What is the difference between discretionary access control (DAC) and role-based access control (RBAC)?
An employee of a company receives an email with an attachment. They notice that this email is from a suspicious source, and they decide not to open the attached file. After further investigation, a security analyst concludes that this file is malware. To which category of the Cyber Kill Chain model does this event belong?
An engineer must gather data for monitoring purposes from different network devices. The engineer needs to collect events from the local network and use that information for packet sniffing. The solution must create an exact copy of traffic and provide full fidelity. Which solution should the engineer use?
An engineer receives a security alert that traffic with a known TOR exit node has occurred on the network. What is the impact of this traffic?
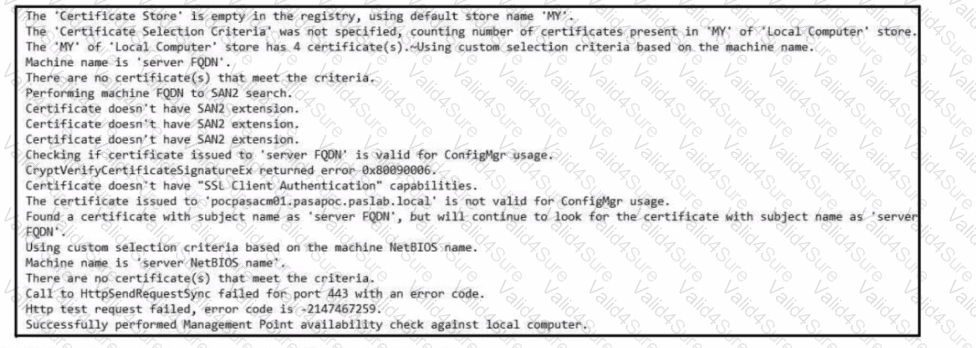
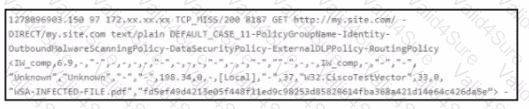
Refer to the exhibit. Which set of actions must an engineer perform to identify and fix this issue?
The SOC team detected an ongoing port scan. After investigation, the team concluded that the scan was targeting the company servers. According to the Cyber Kill Chain model, which step must be assigned to this type of event?