PPAN01 Exam Dumps - Certified Threat Protection Analyst Exam
Searching for workable clues to ace the Proofpoint PPAN01 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s PPAN01 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
What is a defining characteristic of Advanced Persistent Threat (APT) actors?
Which two tasks are considered frequent and high-priority when actively reviewing the threat landscape? (Select two.)
Refer to the exhibit.
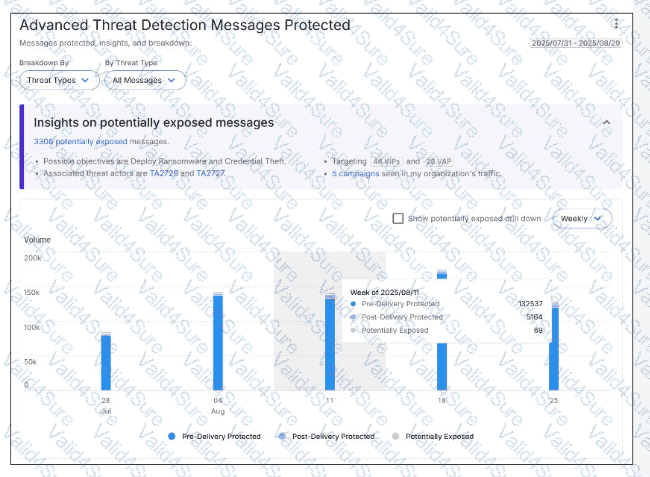
Based on the metrics for the highlighted week, how many malicious messages were blocked by TAP at the email gateway?
As a security analyst, you need to update the TAP URL Defense Custom Blocklist. Which three entries are valid formats for the blocklist? (Select three.)
An analyst has been tasked with providing a report that can be used to prioritise investigations based on a user's Attack Index score. Which report would be most suitable for this purpose?
For which two reasons should organizations customize their incident response plans based on NIST SP 800-61 or another incident response standard? (Select two.)
What happens when a user clicks a rewritten URL that TAP URL Defense has determined to be malicious?