F5CAB5 Exam Dumps - BIG-IP Administration Support and Troubleshooting (F5CAB5) exam
Searching for workable clues to ace the F5 F5CAB5 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s F5CAB5 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
A user needs to determine known security vulnerabilities on an existing BIG-IP appliance and how to remediate these vulnerabilities. Which action should the BIG-IP Administrator recommend?
A BIG-IP Administrator adds new Pool Members into an existing, highly utilized pool. Soon after, there are reports that the application is failing to load for some users. What pool level setting should the BIG-IP Administrator check?
Refer to the exhibit.
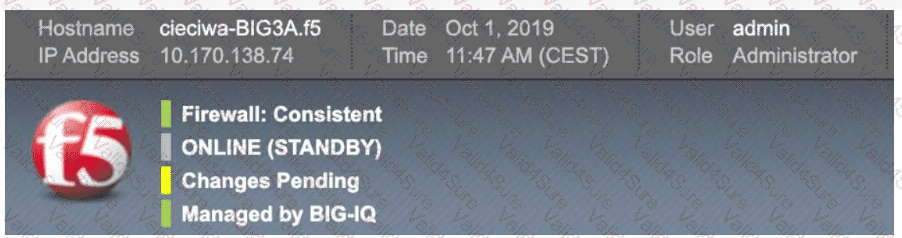
The BIG-IP Administrator has modified an iRule on one device of an HA pair. The BIG-IP Administrator notices there is NO traffic on the BIG-IP device in which they are logged into. What should the BIG-IP Administrator do to verify if the iRule works correctly?