TPAD01 Exam Dumps - Threat Protection Administrator Exam
Searching for workable clues to ace the Proofpoint TPAD01 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s TPAD01 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
Refer to the exhibit to see the interface used in this scenario.
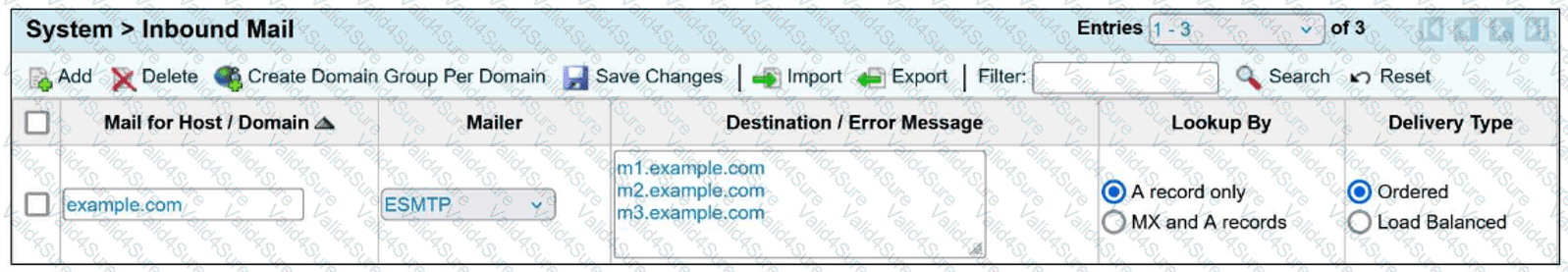
Which of the following is true regarding the inbound mail route?
What are the three default methods available in Recipient Verification to verify that a recipient mailbox exists?
Pick the 3 correct responses below.