SC-200 Exam Dumps - Microsoft Security Operations Analyst
Searching for workable clues to ace the Microsoft SC-200 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s SC-200 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
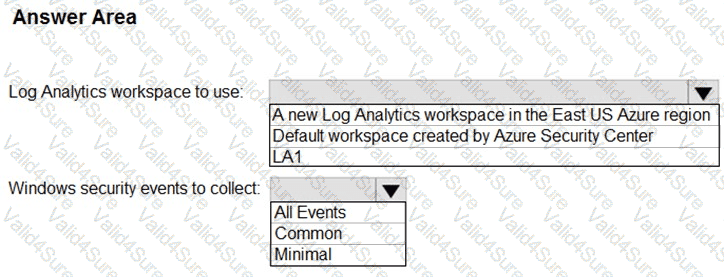
You need to implement Azure Defender to meet the Azure Defender requirements and the business requirements.
What should you include in the solution? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
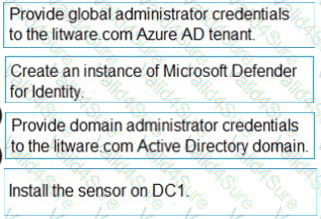
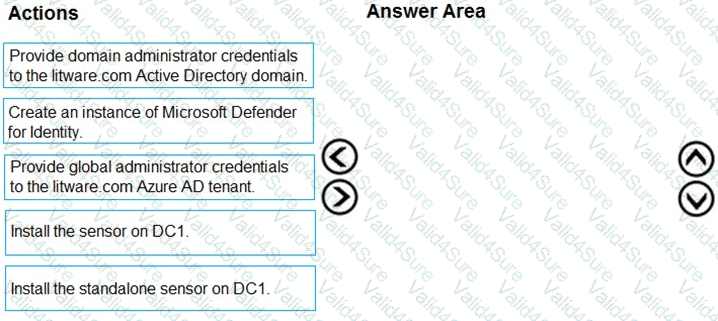
You need to configure DC1 to meet the business requirements.
Which four actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
You need to modify the anomaly detection policy settings to meet the Cloud App Security requirements. Which policy should you modify?
Your on-premises network contains two Active Directory Domain Services (AD DS) domains named contoso.com and fabrikam.com. Contoso.com contains a group named Group1. Fabrikam.com contains a group named Group2.
You have a Microsoft Sentinel workspace named WS1 that contains a scheduled query rule named Rule1. Rule1 generates alerts in response to anomalous AD DS security events. Each alert creates an incident.
You need to implement an incident triage solution that meets the following requirements:
· Security incidents from contoso.com must be assigned to Group1.
· Security incidents from fabrikam.com must be assigned to Group2.
· Administrative effort must be minimized.
What should you include in the solution?
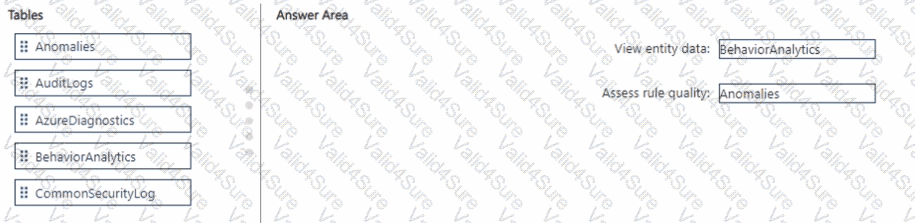
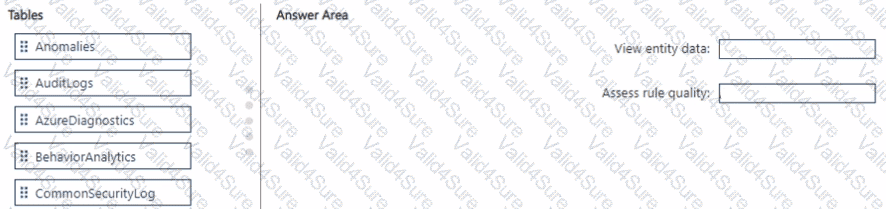
You have a Microsoft Sentinel workspace named SW1.
In SW1. you enable User and Entity Behavior Analytics (UEBA).
You need to use KQL to perform the following tasks:
• View the entity data that has fields for each type of entity.
• Assess the quality of rules by analyzing how well a rule performs.
Which table should you use in KQL for each task? To answer, drag the appropriate tables to the correct tasks. Each table may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
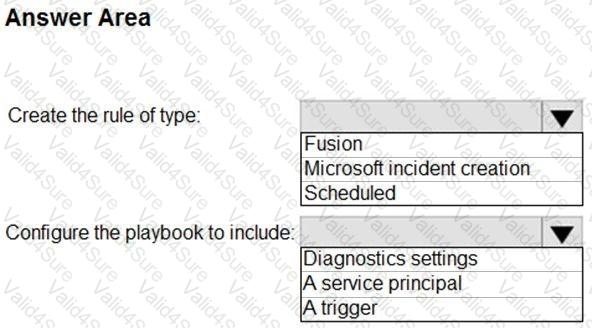
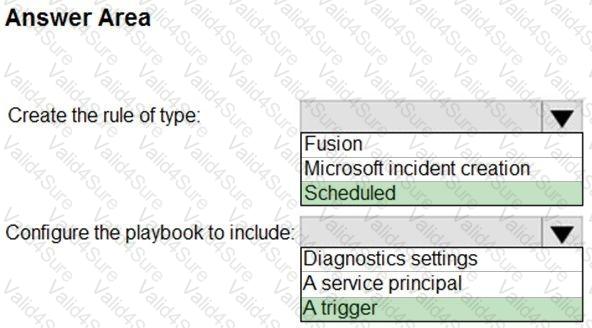
You need to create the test rule to meet the Azure Sentinel requirements. What should you do when you create the rule?
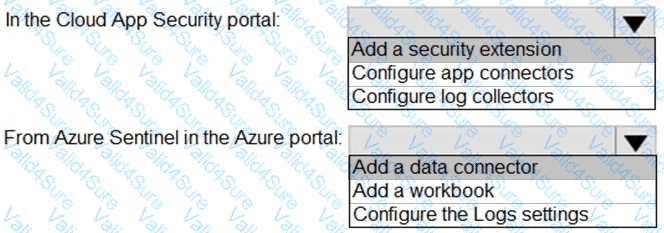
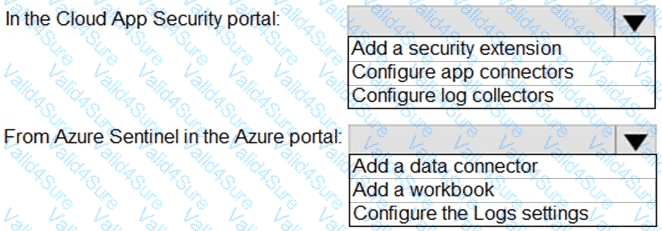
You need to configure the Azure Sentinel integration to meet the Azure Senti nel requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
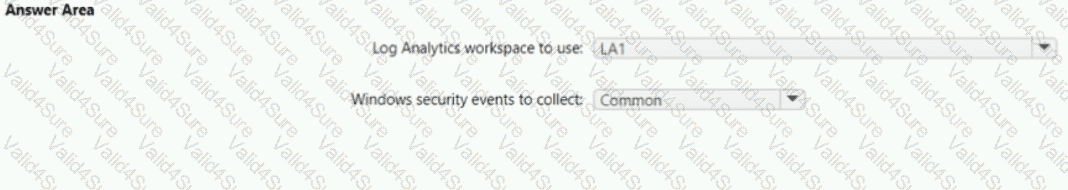
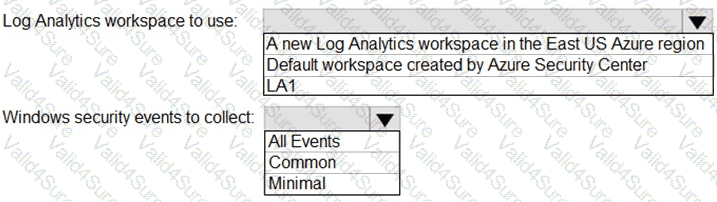
You need to implement Microsoft Defender for Cloud to meet the Microsoft Defender for Cloud requirements and the business requirements. What should you include in the solution? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.