CAS-004 Exam Dumps - CompTIA SecurityX Certification Exam
Searching for workable clues to ace the CompTIA CAS-004 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s CAS-004 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
A company would like to move its payment card data to a cloud provider. Which of the following solutions will best protect account numbers from unauthorized disclosure?
A web application server is running a legacy operating system with an unpatched RCE (Remote Code Execution) vulnerability. The server cannot be upgraded until the corresponding application code is updated. Which of the following compensating controls would prevent successful exploitation?
A CRM company leverages a CSP PaaS service to host and publish its SaaS product. Recently, a large customer requested that all infrastructure components must meet strict regulatory requirements, including configuration management, patch management, and life-cycle management. Which of the following organizations is responsible for ensuring those regulatory requirements are met?
An engineer has had scaling issues with a web application hosted on premises and would like to move to a serverless architecture. Which of the following cloud benefits would be best to utilize for this project?
An organization has severallegacy systemsthat are critical to testing currently deployed assets. These systems have become aserious riskto the organization's security posture, and the securitymanager must implement protection measures to preventcritical infrastructurefrom being impacted. The systems must stayinterconnectedto allow communication with the deployed assets. Which of the following designs, if implemented, woulddecrease the most risksbut still meet the requirements?
An administrator completed remediation for all the findings of a penetration test and notifies the management team that the systems are ready to be placed back into production. Which of the following steps should the management team require the analyst to perform immediately before placing the systems back into production?
A security architect is improving a healthcare organization's security posture. Most of the software is cloud-based, but some old applications are still running on a server on-site. Medical devices using such applications require very low latency. The most important consideration isconfidentiality, followed byavailability, and thenintegrity. Which of the following is thefirst stepthe security architect should implement to protect PII?
A security architect examines a section of code and discovers the following:
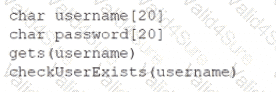
Which of the following changes should the security architect require before approving the code for release?