312-39 Exam Dumps - Certified SOC Analyst (CSA v2)
Searching for workable clues to ace the ECCouncil 312-39 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s 312-39 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
According to the Risk Matrix table, what will be the risk level when the probability of an attack is very low and the impact of that attack is major?
According to the forensics investigation process, what is the next step carried out right after collecting the evidence?
Properly applied cyber threat intelligence to the SOC team help them in discovering TTPs.
What does these TTPs refer to?
What is the process of monitoring and capturing all data packets passing through a given network using different tools?
A financial institution's SIEM is generating a high number of false positives, causing alert fatigue among SOC analysts. To reduce this burden and improve threat detection accuracy, the organization integrates AI capabilities into the SIEM. After implementation, the SOC team observes a significant decrease in redundant alerts, along with faster detection of genuine threats. Which AI capability contributed to this improvement?
Harley is working as a SOC analyst with Powell Tech. Powell Inc. is using Internet Information Service (IIS) version 7.0 to host their website.
Where will Harley find the web server logs, ifhe wants to investigate them for any anomalies?
Jony, a security analyst, while monitoring IIS logs, identified events shown in the figure below.
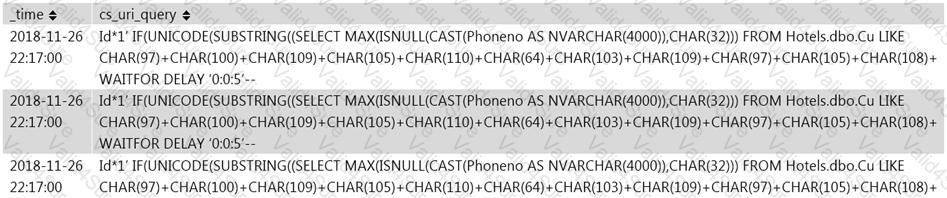
What does this event log indicate?