200-201 Exam Dumps - Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)
Searching for workable clues to ace the Cisco 200-201 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s 200-201 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
During which phase of the forensic process is data that is related to a specific event labeled and recorded to preserve its integrity?
What is a key difference between a tampered and an untampered disk image during a forensic investigation?
Which type of evasion technique is accomplished by separating the traffic into smaller segments before transmitting across the network?
Which principle reduces the risk of attackers gaining access to sensitive data by compromising a low-level user account?
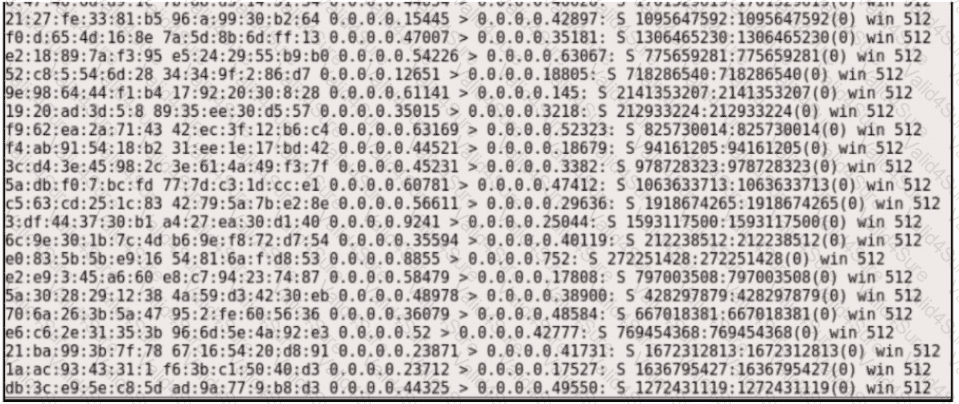
Which two protocols are used for DDoS amplification attacks? (Choose two.)