1Y0-440 Exam Dumps - Architecting a Citrix Networking Solution
Searching for workable clues to ace the Citrix 1Y0-440 Exam? You’re on the right place! ExamCert has realistic, trusted and authentic exam prep tools to help you achieve your desired credential. ExamCert’s 1Y0-440 PDF Study Guide, Testing Engine and Exam Dumps follow a reliable exam preparation strategy, providing you the most relevant and updated study material that is crafted in an easy to learn format of questions and answers. ExamCert’s study tools aim at simplifying all complex and confusing concepts of the exam and introduce you to the real exam scenario and practice it with the help of its testing engine and real exam dumps
Scenario: A Citrix Architect needs to assess a Citrix Gateway deployment that was recently completed by a customer and is currently in pre-production testing. The Citrix Gateway needs to use ICA proxy to provide access to a Citrix Virtual Apps and Citrix Virtual Desktops environment. During the assessment, the customer informs the architect that users are NOT able to launch published resources using the Gateway virtual server.
Click the Exhibit button to view the troubleshooting details collected by the customer.
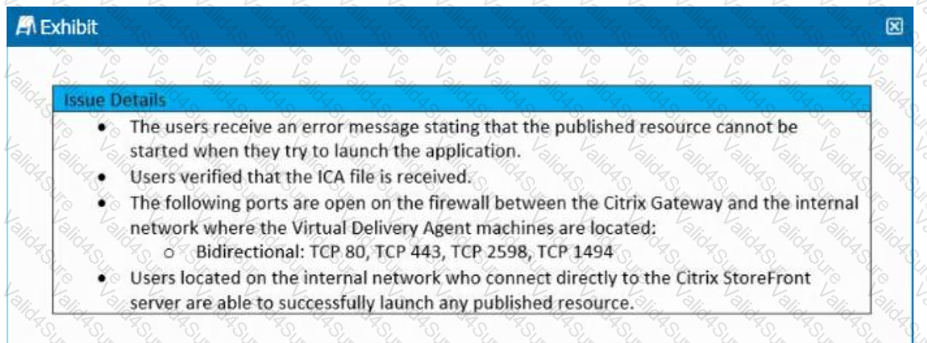
What is the cause of this issue?
Scenario: A Citrix Engineer is asked by management at the workspacelab organization to review their existing Citrix ADC Configurations and make the necessary upgrades. The architect recommends small changes to the pre-existing Citrix ADC configuration. Currently, the Citrix ADC MPX devices are configured in high-availability pair, and the outbound traffic is load balanced between two internet service providers (ISPs), however, the failover is NOT happening correctly. The following requirements were discussed during the design requirement phase:
- The return traffic for a specific flow should be routed through the same path while using Link Load Balancing.
- The link should fail over even if the ISP router is up and intermediary devices to an ISP router are down.
- Traffic going through one ISP router should fail over to the secondary ISP, and the traffic should not flow through both routers simultaneously.
What should the architect configure with Link Load Balancing LLB) to meet the requirement?
Scenario: A Citrix Architect has implemented two high availability pairs of MPX 5500 and MPX 11500 devices respectively with 12.0.53.13 nc version. The NetScaler devices are set up to handle NetScaler Gateway, Load Balancing, Application Firewall, and Content Switching. The Workspacelab infrastructure is set up to be monitored with NMAS version 12.0.53.13 nc by the Workspacelab administrators. The Workspacelab team wants to implement one more pair of NetScaler MPX 7500 devices with version 12.0.53.13 nc.
The Citrix consulting team has assigned the task to implement these NetScaler devices in the infrastructure and set them up to be monitored and managed by NMAS.
The following are the requirements that were discussed during the project initiation call:
- NMAS should be configured to get the infrastructure information under sections such as HDX Insight, WEB Insight, and Security Insight.
- Configuration on the new MPX devices should be identical to MPX 11500 devices.
- Configuration changes after the deployment and initial setup should be optimized using NMAS.
- NMAS should be utilized to configure templates that can be utilized by the Workspacelab team in future deployment.
- As per the requirement from the Workspacelab team, NMAS should be store the audited data for only 15 days.
Which process should the architect utilize to ensure that the deployment of MPX 11500 devices are optimized and that it is correct, before deploying the devices in production?
Which encoding type can a Citrix Architect use to encode the StyleBook content, when importing the StyleBook configuration under source attribute?
Scenario: The Workspacelab team has configured their NetScaler Management and Analytics (NMAS) environment. A Citrix Architect needs to log on to the NMAS to check the settings.
Which two authentication methods are supported to meet this requirement? (Choose two.)